Researchers find another smart toy that's easy to hack
 A team of security researchers that has warned of the dangers of smart toys has found another that can be used to spy on your children. Pen Test Partners examined the Teksta Toucan, finding that it's easy to hack the device's microphone and speaker.
A team of security researchers that has warned of the dangers of smart toys has found another that can be used to spy on your children. Pen Test Partners examined the Teksta Toucan, finding that it's easy to hack the device's microphone and speaker.
The device is built by Genesis Industries, makers of the iQue and My Friend Cayla, two devices that are already feeling the heat from regulators. Both are currently being looked at in the US and Europe, while the latter has been withdrawn from sale in Germany. The Toucan had two ways of being accessed, the first of which was simply by connecting to the device's built-in Bluetooth speaker.
Read moreStrangers can talk to your child through 'connected' toys
 A consumer group is urging major retailers to withdraw a number of “connected” or “intelligent” toys likely to be popular at Christmas, after finding security failures that it warns could put children’s safety at risk.
A consumer group is urging major retailers to withdraw a number of “connected” or “intelligent” toys likely to be popular at Christmas, after finding security failures that it warns could put children’s safety at risk.
Tests carried out by Which? with the German consumer group Stiftung Warentest, and other security research experts, found flaws in Bluetooth and wifi-enabled toys that could enable a stranger to talk to a child. The investigation found that four out of seven of the tested toys could be used to communicate with the children playing with them. Security failures were discovered in the Furby Connect, i-Que Intelligent Robot, Toy-Fi Teddy and CloudPets.
Read moreGoogle Nest: Unpatched bug lets intruders use Bluetooth to stop cameras recording
 A researcher has flagged a bug in Google's Nest Cam and Dropcam Pro security cameras that allows an attacker within Bluetooth range to stop either device from recording.
A researcher has flagged a bug in Google's Nest Cam and Dropcam Pro security cameras that allows an attacker within Bluetooth range to stop either device from recording.
Bluetooth range, of course, is exactly where a burglar would be when planning to ransack a home, and with attack code now publicly available, an intruder could knock Google's security cameras off a wireless network for 90 seconds. That mightn't sound so severe, but since the camera is designed to only store recorded footage in the cloud, the loss of connectivity means the device loses its surveillance capabilities for this period.
Read moreGoogle, Levi's to release smart jacket in the fall
 Google and Levi's first announced Project Jacquard back in June 2015, promising smart clothes that would be capable of interacting with the mobile devices of the wearer.
Google and Levi's first announced Project Jacquard back in June 2015, promising smart clothes that would be capable of interacting with the mobile devices of the wearer.
Almost two years later, the unlikely partnership has now revealed that a smart jacket named the Commuter will be released into the market in the fall, with a price tag of $350. The Commuter jacket was unveiled by Google and Levi's in May of last year at the Google I/O conference as the first product under Project Jacquard. More details regarding the smart clothing was unveiled at SXSW 2017, including its price tag of $350 once it is launched in the fall.
Read moreApple is working on smart glasses
 Apple Inc. is weighing an expansion into digital glasses, a risky but potentially lucrative area of wearable computing, according to people familiar with the matter. While still in an exploration phase, the device would connect wirelessly to iPhones, show images and other information in the wearer’s field of vision, and may use augmented reality, the people said.
Apple Inc. is weighing an expansion into digital glasses, a risky but potentially lucrative area of wearable computing, according to people familiar with the matter. While still in an exploration phase, the device would connect wirelessly to iPhones, show images and other information in the wearer’s field of vision, and may use augmented reality, the people said.
They asked not to be identified speaking about a secret project. Apple has talked about its glasses project with potential suppliers, according to people familiar with those discussions. The company has ordered small quantities of near-eye displays from one supplier for testing, the people said.
Read moreFitbit trackers can be hacked in 10 seconds
![]() A vulnerability in FitBit fitness trackers first reported to the vendor in March could still be exploited by the person you sit next to on a park bench while catching your breath.
A vulnerability in FitBit fitness trackers first reported to the vendor in March could still be exploited by the person you sit next to on a park bench while catching your breath.
The athletic-achievement-accumulating wearables are wide open on their Bluetooth ports, according to research by Fortinet. The attack is quick, and can spread to other computers to which an infected FitBit connects. Attacks over Bluetooth require an attacker hacker to be within metres of a target device. This malware can be delivered 10 seconds after devices connect, making even fleeting proximity a problem. Testing the success of the hack takes about a minute, although it is unnecessary for the compromise.
Read moreHackers target smart bracelets
 This story began a few months ago when I got a popular brand of fitness bracelet. As this is a wearable device I installed Android Wear app, an application developed especially for wearable devices. This application easily connects to the fitness band.
This story began a few months ago when I got a popular brand of fitness bracelet. As this is a wearable device I installed Android Wear app, an application developed especially for wearable devices. This application easily connects to the fitness band.
However, there was something odd: the program could connect to a Nike+ Fuel Band SE, but my bracelet was another brand! It wasn't long before I realized my colleague had a Nike wristband – and he didn't even notice I had connected to his device. After that I decided to do some research and find out how secure my wristband was. Smart bracelets: communication with a smartphone.
Read moreCould your heartbeat replace your bank pin?
 Anyone who banks online will know how difficult it can sometimes be to remember multiple passwords and pin numbers on a daily basis. Halifax believes it could have a solution: a wristband that identifies customers by their heartbeat.
Anyone who banks online will know how difficult it can sometimes be to remember multiple passwords and pin numbers on a daily basis. Halifax believes it could have a solution: a wristband that identifies customers by their heartbeat.
Apparently everyone has a unique heart rhythm, which can be used to identify us much in the same way as fingerprints. Customers would put the band on their wrists, which measures their electrocardiogram or ECG. The ECG data is read when a customer wears the band on one wrist and touches the top sensor with a finger on the other hand.
Read moreThe Bluewire Is A Bluetooth Headset That Can Record Your Calls
 Journalists, PR folk, and anyone else who needs accurate copies of calls over the phone or Skype should check out a new Bluetooth headset. Nowadays there are plenty of headsets out there that give you a comfortable fit or decent sound quality compared to the earbuds that come with our phones, the Bluewire actually can even record conversations.
Journalists, PR folk, and anyone else who needs accurate copies of calls over the phone or Skype should check out a new Bluetooth headset. Nowadays there are plenty of headsets out there that give you a comfortable fit or decent sound quality compared to the earbuds that come with our phones, the Bluewire actually can even record conversations.
You don’t even have to make your calls and communicate over the headset. As long as it’s paired to your smartphone, it will record both sides of a conversation, even if it takes place over a different headset you find more comfortable or your in-car audio system.
Read moreHackers know how to access data sent between smartphones and smartwatches
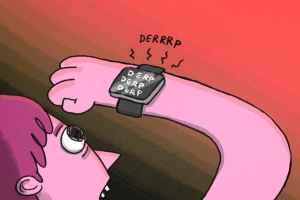 Security experts at BitDefender demonstrated how is possible to access data exchanged between a smartwatch and a smartphone. The paradigm of Internet of Things is influencing modern society and the way it approaches the technology in everyday life.
Security experts at BitDefender demonstrated how is possible to access data exchanged between a smartwatch and a smartphone. The paradigm of Internet of Things is influencing modern society and the way it approaches the technology in everyday life.
An impressive amount of Intelligent devices surround us, but often we ignore the repercussion in term of security and privacy. The IoT devices are designed to improve our experience with technology, but we must consider thta they enlarge our surface of attack. Today we will discuss the risk related to the use of a Smartwatch that is able to dialog with an Android smartphone.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















