Hacker beats Galaxy S8 iris scanner using an IR image and a contact lens
 Based on name alone, the futuristic iris-scanning feature on the Galaxy S8 sounds like it would be the most secure way to lock your phone. Hacker Jan Krissler, who goes by the name Starbug, shows in a recent video that, despite the impressive technology in unlocking your phone with your eyes, the security system can be beaten with a relatively low-tech hack.
Based on name alone, the futuristic iris-scanning feature on the Galaxy S8 sounds like it would be the most secure way to lock your phone. Hacker Jan Krissler, who goes by the name Starbug, shows in a recent video that, despite the impressive technology in unlocking your phone with your eyes, the security system can be beaten with a relatively low-tech hack.
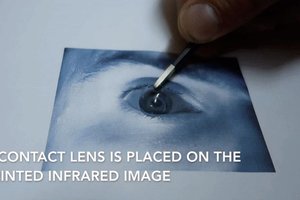
As the video shows, Starbug is able to take a infrared picture of a person’s face using the night mode setting on a regular point and shoot camera. Print it out on an ordinary laser printer and it fools the camera by placing a contact lens over the image to give it the appearance of an actual human eye.
Read moreMost disruptive cyberattacks against UK firms not reported to public
 Cyberattacks against businesses operating in the UK are more prevalent than ever yet many customers may never become aware about major hacking incidents as the majority of firms are not required by law to report breaches to public bodies.
Cyberattacks against businesses operating in the UK are more prevalent than ever yet many customers may never become aware about major hacking incidents as the majority of firms are not required by law to report breaches to public bodies.
Survey results released by DCMS stated that "nearly half" of UK firms sampled had identified a "breach or attack" in the last year. It was carried out by Ipsos Mori and included 1,523 UK-based businesses in total. "While breaches do not always result in a material outcome, such as loss of data or network access, in cases where this does happen, it has a significant impact on the organisation," it warned.
Read moreSamsung joins the self-driving car gold rush
 The tech industry has a bad case of four-wheel fever, and it looks like there's no cure in sight. Before too long, it will be impossible to buy a new car without an embedded LTE modem—ostensibly there for our convenience, but with the side effect of creating a new revenue stream from monetized data.
The tech industry has a bad case of four-wheel fever, and it looks like there's no cure in sight. Before too long, it will be impossible to buy a new car without an embedded LTE modem—ostensibly there for our convenience, but with the side effect of creating a new revenue stream from monetized data.
And then there's the self-driving car gold rush. Anyone who's anyone in the tech or automotive worlds is working on an autonomous vehicle, a list that now includes Samsung. The company has been granted permission by the South Korean government to begin testing an autonomous vehicle on public roads.
Read moreThe Galaxy S8’s facial scanner can be tricked with a photo
 Samsung just recently took the wraps off its latest flagship, the Galaxy S8. In addition to the super-slim bezels, tall screen, and speedy new Snapdragon 835 (or Exynos 9) processor, the device is also coming with a ton of biometric authentication options. You get a fingerprint reader, iris recognition, and face recognition.
Samsung just recently took the wraps off its latest flagship, the Galaxy S8. In addition to the super-slim bezels, tall screen, and speedy new Snapdragon 835 (or Exynos 9) processor, the device is also coming with a ton of biometric authentication options. You get a fingerprint reader, iris recognition, and face recognition.
With the public's first exposure to the Galaxy S8 happening a few days ago, it was only a matter of time until one of these biometric solutions had some holes poked in it. One of those holes is that Galaxy S8's face recognition can be tricked with a photo. At least this is what a video from Spanish Periscope user Marcianophone purports.
Read moreWhatsApp must be accessible to authorities, says Amber Rudd
 Amber Rudd has called for the police and intelligence agencies to be given access to WhatsApp and other encrypted messaging services to thwart future terror attacks, prompting opposition politicians and civil liberties groups to say her demand was unrealistic and disproportionate.
Amber Rudd has called for the police and intelligence agencies to be given access to WhatsApp and other encrypted messaging services to thwart future terror attacks, prompting opposition politicians and civil liberties groups to say her demand was unrealistic and disproportionate.
The home secretary said it was “completely unacceptable” that the government could not read messages protected by end-to-end encryption and said she had summoned leaders of technology companies to a meeting to discuss what to do. Rudd refused to rule out passing new legislation to tackle encrypted messaging if she did not get what she wanted.
Read moreWikiLeaks reveals the CIA hacked into Apple iPhones, Google Android phones and Samsung TVs
 Tech giants Apple, Samsung and Microsoft have broken their silence on the latest leak from WikiLeaks that revealed the CIA hacked into their products for surveillance purposes. Apple claimed to have previously addressed the vulnerabilities in their operating system, iOS, revealed in Tuesday’s ‘Vault 7’ leak from WikiLeaks.
Tech giants Apple, Samsung and Microsoft have broken their silence on the latest leak from WikiLeaks that revealed the CIA hacked into their products for surveillance purposes. Apple claimed to have previously addressed the vulnerabilities in their operating system, iOS, revealed in Tuesday’s ‘Vault 7’ leak from WikiLeaks.
“While our initial analysis indicates that many of the issues leaked today were already patched in the latest iOS, we will continue work to rapidly address any identified vulnerabilities,” the company said in a statement, urging customers to update to the latest version of iOS to ensure they have the most recent security updates.
Read morePreviously unseen malware behind cyberattack against UK's biggest hospital group
 A malware attack which forced parts of the UK's largest hospital group offline has been blamed on a new form of malware, which bypassed antivirus software and infected the network.
A malware attack which forced parts of the UK's largest hospital group offline has been blamed on a new form of malware, which bypassed antivirus software and infected the network.
A January cyberattack against Barts Health NHS Trust -- which incorporates five East London hospitals, 15,000 staff, and provides care to millions of patients a year -- resulted in a number of computer systems being shut down as a precaution. s a result of the attack, the Barts Health pathology system was taken offline before eventually being restored a few days later. The hospital said the virus didn't gain access to patient data.
Read moreNew skimmers fit right on top of chip and PIN credit card scanners
 Mr. Krebs has some great images of a credit card skimmer found in the wild. This model uses Samsung phone parts and lays right over the Ingenico card scanners you’ve probably seen in stores.
Mr. Krebs has some great images of a credit card skimmer found in the wild. This model uses Samsung phone parts and lays right over the Ingenico card scanners you’ve probably seen in stores.
The interesting thing is that these scanners also support chip and PIN technology but, as evidenced by the photo, it looks like the retailer disabled it essentially sending the scanner back into the 1970s and allowed the skimmer unfettered access. Chip and PIN scanners are ostensibly safer and therefore card skimmers have to work harder to get the goods. The particular model is quite realistic and automatically dumps data to a nearby Bluetooth device.
Read moreAndroid phones could be vulnerable to a fricking WAP attack
 Someone send Samsung's pr people some biscuits or something, they could do with a break.
Someone send Samsung's pr people some biscuits or something, they could do with a break.
Not only have the poor bastards had to endure the news that the company that they work for released a phone that can catch fire, but now a security firm called Context says that its Galaxy phones are vulnerable to an SMS attack that can be triggered remotely and turn users' devices into the sort of thing that young people in pyjamas are supposed to rescue from the floor of swimming pools. A brick. Context starts by telling us that Android phones are vulnerable to these SMS attacks and that the victim will be subjected to ransomware shakedowns.
Read moreHackers can remotely access your Samsung SmartСam security cameras
 It's not necessary to break into your computer or smartphone to spy on you. Today all devices in our home are becoming more connected to networks than ever to make our lives easy.
It's not necessary to break into your computer or smartphone to spy on you. Today all devices in our home are becoming more connected to networks than ever to make our lives easy.
But these connected devices can be turned against us, anytime, due to lack of stringent security measures and insecure encryption mechanisms implemented in these IoT devices. The most recent victim of this issue is the Samsung's range of SmartCam home security cameras. Yes, it's easy to hijack the popular Samsung SmartCam security cameras, as they contain a critical remote code execution vulnerability that could let hackers take full control of these devices.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















