Snowden files 'read by Russia and China': five questions for UK government
 The Sunday Times produced what at first sight looked like a startling news story: Russia and China had gained access to the cache of top-secret documents leaked by former NSA contractor turned whistleblower Edward Snowden.
The Sunday Times produced what at first sight looked like a startling news story: Russia and China had gained access to the cache of top-secret documents leaked by former NSA contractor turned whistleblower Edward Snowden.
Not only that, but as a result, Britain’s overseas intelligence agency, the Secret Intelligence Service, better known as MI6, had been forced “to pull agents out of live operations in hostile countries”. These are serious allegations and, as such, the government has an obligation to respond openly. The story is based on sources including “senior officials in Downing Street, the Home Office and the security services”.
Read moreNSA spied on non-American anti-virus companies
 British and American intelligence agencies have spied on anti-virus companies and probed their software for weaknesses, as the snoops sought to enhance their offensive surveillance techniques.
British and American intelligence agencies have spied on anti-virus companies and probed their software for weaknesses, as the snoops sought to enhance their offensive surveillance techniques.
This was predictable given previous revelations around the extensive hacking capabilities at GCHQ and the NSA, but for reasons not outlined in the leaks or by the agencies themselves, notable US and UK anti-virus providers were seemingly left untouched, despite being used across the world. Older versions of F-Secure also used the Kaspersky signature database, which contained lists of blacklisted malware.
Read moreNew exploit turns Samsung Galaxy phones into remote bugging devices
 As many as 600 million Samsung phones may be vulnerable to attacks that allow hackers to surreptitiously monitor the camera and microphone, read incoming and outgoing text messages, and install malicious apps.
As many as 600 million Samsung phones may be vulnerable to attacks that allow hackers to surreptitiously monitor the camera and microphone, read incoming and outgoing text messages, and install malicious apps.
When downloading updates, the Samsung devices don't encrypt the executable file, making it possible for attackers in a position to modify upstream traffic — such as those on the same Wi-Fi network — to replace the legitimate file with a malicious payload. The exploit was demonstrated at the Blackhat security conference in London by Ryan Welton, a researcher with security firm NowSecure.
Read moreCampaigners challenge GCHQ data collection practices
 Campaigners have filed a legal claim with the Investigatory Powers Tribunal that could end bulk data interception by UK intelligence agencies. UK charity Privacy International has filed the claim, arguing that GCHQ should end the bulk collection of data, which recently became illegal in the US with the passing of last week’s Freedom Act.
Campaigners have filed a legal claim with the Investigatory Powers Tribunal that could end bulk data interception by UK intelligence agencies. UK charity Privacy International has filed the claim, arguing that GCHQ should end the bulk collection of data, which recently became illegal in the US with the passing of last week’s Freedom Act.
The organisation claims that it has made the first UK legal challenge to bulk data collection, and notes that the equivalent NSA power has now been curtailed before the debate this side of the pond has even begun. It has criticised the fact that GCHQ is operating with “no proper legal regime in place.
Read moreNine in 10 top firms hit by cyber attacks
 Cyber-criminals have attacked 90 per cent of major British companies – costing the economy tens of billions of pounds, it emerged. Figures reveal that the threat from hackers trying to steal confidential data is rising steeply.
Cyber-criminals have attacked 90 per cent of major British companies – costing the economy tens of billions of pounds, it emerged. Figures reveal that the threat from hackers trying to steal confidential data is rising steeply.
Experts warned the typical cost to big firms of the most severe information security breaches had nearly tripled. The country faces advanced and persistent threats every day, a top official at the GCHQ spy agency warned. The attacks show little sign of abating and include threats from hostile states, terror groups and malicious hackers known as hacktavists.
Read moreHuman error to blame as UK data breach investigations surge
 UK data breach investigations within the financial services industry almost trebled over the last two years, according to security figures acquired via a Freedom of Information request to the Information Commissioner’s Office, with human error almost always responsible.
UK data breach investigations within the financial services industry almost trebled over the last two years, according to security figures acquired via a Freedom of Information request to the Information Commissioner’s Office, with human error almost always responsible.
The figures come during a period of increased scrutiny of how the financial services industry handles confidential personal and corporate data. Most recently, the Bank of England was revealed to have inadvertently sent sensitive financial information regarding contingency plans if the UK left the EU to the wrong email address. Human error was blamed for the vast majority of the breaches.
Read moreInternet troll convictions are on the rise
 Convictions for crimes under a law used to prosecute internet "trolls" have increased ten-fold in a decade with five a day, official figures reveal.
Convictions for crimes under a law used to prosecute internet "trolls" have increased ten-fold in a decade with five a day, official figures reveal.
The new figures revealed a similar rise in the number of convictions under the Malicious Communications Act, which states that it is an offence to send a threatening, offensive or indecent letter, electronic communication, message or article with the intent to cause distress or anxiety. It is a crime under the Communications Act to send by means of a public electronic communications network a message or other material that is grossly offensive or of an indecent, obscene or menacing character.
Read moreFactory reset in Android phones leaves sensitive user data behind
 It's common sense to reset an Android phone to its factory state before selling or disposing of it. But beware, security researchers recently found that this often fails to properly wipe all sensitive user data from the device.
It's common sense to reset an Android phone to its factory state before selling or disposing of it. But beware, security researchers recently found that this often fails to properly wipe all sensitive user data from the device.
A test on 21 second-hand smartphones running Android versions between 2.3.x and 4.3 revealed that it's possible to recover emails, text messages, Google access tokens and other sensitive data after the factory reset function had been used. The study was done by researchers Laurent Simon and Ross Anderson from the University of Cambridge in the UK on used devices bought from eBay between January and May 2014.
Read moreIs the internet on the brink of collapse?
 The internet is heading towards a capacity crunch as it fails to keep up with our demand for ever faster data, scientists have warned. Leading engineers, physicists and telecoms firms have been summoned to a meeting to discuss what can be done to avert a web crisis.
The internet is heading towards a capacity crunch as it fails to keep up with our demand for ever faster data, scientists have warned. Leading engineers, physicists and telecoms firms have been summoned to a meeting to discuss what can be done to avert a web crisis.
The boom of internet television, streaming services and ever-more powerful computers has increased the strain on our communications infrastructure. In just 20 years, if usage rates continue, all of Britain's power supply could be consumed by internet use. The cables and fibre optics that send information to our laptops, smartphones and tablets will have reached their limit to send data within eight years, experts warn.
Read moreSamsung Galaxy S5 flaw allows hackers to clone fingerprints
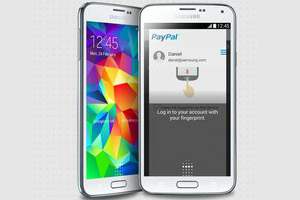 Biometric information is about as personal as data gets. But Google’s Android partners are still failing to protect it, as researchers will discuss this week at RSA, pointing to failures in the Samsung Galaxy S5 and other unnamed Android devices.
Biometric information is about as personal as data gets. But Google’s Android partners are still failing to protect it, as researchers will discuss this week at RSA, pointing to failures in the Samsung Galaxy S5 and other unnamed Android devices.
Though the affected phone makers have tried to separate and encrypt the information in a separate secure zone, it’s possible to grab the biometric data before it reaches that protected area and create copies of people’s fingerprints for further attacks. The issue appears startlingly straightforward: an attacker could focus on collecting data coming from the Android devices’ fingerprint sensors rather than trying to break into the trusted zone. Any hacker who can acquire user-level access can easily collect fingerprint information from the affected Android phones.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















