NSA helped British spies find security holes in Juniper Firewalls
 A top-secret document dated reveals that British spy agency GCHQ, with the knowledge and apparent cooperation of the NSA, acquired the capability to covertly exploit security vulnerabilities in 13 different models of firewalls made by Juniper Networks.
A top-secret document dated reveals that British spy agency GCHQ, with the knowledge and apparent cooperation of the NSA, acquired the capability to covertly exploit security vulnerabilities in 13 different models of firewalls made by Juniper Networks.
The six-page document raises questions about whether the intelligence agencies were responsible for or culpable in the creation of security holes disclosed by Juniper last week. The possibility of links between the security holes and the intelligence agencies is particularly important given an ongoing debate in the U.S. and the U.K. over whether governments should have backdoors allowing access to encrypted data.
Read moreA secret catalogue of government gear for spying on your cellphone
 The Intercept has obtained a secret, internal U.S. government catalogue of dozens of cellphone surveillance devices used by the military and by intelligence agencies. The document also offers rare insight into the spying capabilities of federal law enforcement and local police inside the United States.
The Intercept has obtained a secret, internal U.S. government catalogue of dozens of cellphone surveillance devices used by the military and by intelligence agencies. The document also offers rare insight into the spying capabilities of federal law enforcement and local police inside the United States.
The catalogue includes details on the Stingray, a well-known brand of surveillance gear, as well as Boeing “dirt boxes” and dozens of more obscure devices that can be mounted on vehicles, drones, and piloted aircraft. Some are designed to be used at static locations, while others can be discreetly carried by an individual.
Read moreContents of Calyx National Security Letter revealed
 After more than a decade of waiting, the unredacted contents of a National Security Letter filed by the Federal Bureau of Investigation have been made public in court filings surrounding the case of Calyx Internet Access founder Nicholas Merrill who refused to heed the NSL delivered to him 11 years ago.
After more than a decade of waiting, the unredacted contents of a National Security Letter filed by the Federal Bureau of Investigation have been made public in court filings surrounding the case of Calyx Internet Access founder Nicholas Merrill who refused to heed the NSL delivered to him 11 years ago.
Merrill responded in a series of tweets, saying that "The FBI should not be able to silence innocent critics like myself - or hide abuses - simply by saying the magic words 'National Security.'" And he added that "the FBI shouldn't be allowed to demand private customer records without any suspicion of wrongdoing or without any approval from a court."
Read moreFederal judge rules against NSA phone surveillance program
 A federal judge has ruled against the National Security Agency’s collection of Americans’ phone records but the impact is limited because the program is due for major changes by month’s end.
A federal judge has ruled against the National Security Agency’s collection of Americans’ phone records but the impact is limited because the program is due for major changes by month’s end.
U.S. District Court Judge Richard Leon on Monday sided with conservative legal activist Larry Klayman, who had requested a court order barring the NSA from collecting the phone records of some of his clients. The clients had sued the NSA over the data collection following revelations from former NSA contractor Edward Snowden.
Read moreEU politicians want all criminal charges against Edward Snowden dropped
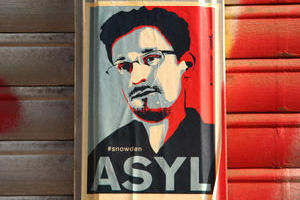 Government-secret leaker Edward Snowden should be granted protection because his leaks were in defense of human rights, the European Parliament said.
Government-secret leaker Edward Snowden should be granted protection because his leaks were in defense of human rights, the European Parliament said.
The parliament passed a nonbinding resolution that called on European Union member states to protect Snowden from "extradition or rendition by third parties" because of "his status as whistle-blower and international human rights defender." The resolution also asks EU countries to drop any criminal charges against Snowden. The former contractor for the US National Security Agency sparked global debate about surveillance in the digital age when he leaked secret NSA documents to journalists in 2013.
Read moreTop German official infected by spy trojan with NSA ties
 German Chancellor Angela Merkel may not be the only high-ranking leader from that country to be spied on by the National Security Agency.
German Chancellor Angela Merkel may not be the only high-ranking leader from that country to be spied on by the National Security Agency.
German authorities are investigating whether the head of the German Federal Chancellery unit had his laptop infected with Regin, a highly sophisticated suite of malware programs that has been linked to the NSA and its British counterpart, the Government Communications Headquarters. Regin is among the most advanced pieces of malware ever discovered, with dozens of modules that can be used to customize attacks on targets in the telecommunications, hospitality, energy, airline, and research industries.
Read moreHow is NSA breaking so much crypto?
 For years, privacy advocates have pushed developers of websites and other cryptographic software to adopt the Diffie-Hellman cryptographic key exchange as a defense against surveillance from the NSA.
For years, privacy advocates have pushed developers of websites and other cryptographic software to adopt the Diffie-Hellman cryptographic key exchange as a defense against surveillance from the NSA.
Researchers are renewing their warning that a serious flaw in the way the key exchange is implemented is allowing the NSA to break and eavesdrop on trillions of encrypted connections. The cost for adversaries is by no means modest. For commonly used 1024-bit keys, it would take about a year and cost a "few hundred million dollars" to crack just one of the extremely large prime numbers that form the starting point of a Diffie-Hellman negotiation.
Read moreEdward Snowden: Smartphones can be taken over
 Smartphone users can do "very little" to stop security services getting "total control" over their devices, Edward Snowden has said. The former intelligence contractor told that UK intelligence agency GCHQ had the power to hack into phones without their owners' knowledge.
Smartphone users can do "very little" to stop security services getting "total control" over their devices, Edward Snowden has said. The former intelligence contractor told that UK intelligence agency GCHQ had the power to hack into phones without their owners' knowledge.
GCHQ could gain access to a handset by sending it an encrypted text message and use it for such things as taking pictures and listening in. Mr Snowden did not suggest that either GCHQ or the NSA were interested in mass-monitoring of citizens' private communications but said both agencies had invested heavily in technology allowing them to hack smartphones.
Read moreEurope-US data transfer deal used by many firms ruled invalid
 The EU's highest court struck down a deal that allows thousands of companies to easily transfer personal data from Europe to the United States.
The EU's highest court struck down a deal that allows thousands of companies to easily transfer personal data from Europe to the United States.
Many companies, both U.S. and European, use the Safe Harbor system to help them get around cumbersome checks to transfer data between offices on both sides of the Atlantic. That includes payroll and human resources information as well as lucrative data used for online advertising, which is of particular importance to tech companies. But the decision by the Court of Justice of the European Union sounds the death knell for the system, set up by the European Commission 15 years ago.
Read moreData sharing deal with US must end due to mass surveillance
 The European Court of Justice's top legal aid has said that a 15-year-old agreement that eases the transfer of data between the EU and the US should be ended, accusing American intelligence services of conducting mass, indiscriminate surveillance.
The European Court of Justice's top legal aid has said that a 15-year-old agreement that eases the transfer of data between the EU and the US should be ended, accusing American intelligence services of conducting mass, indiscriminate surveillance.
The ECJ's advocate-general said that the Safe Harbour agreement does not do enough to protect the private information of EU citizens once it arrives in the US, adding that it should have been suspended. Safe Harbour allows US firms to collect data on their European customers. The system is used by Google, Facebook, and more than 4,000 other companies.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















