Emboldened by $1B Bangladesh hackers, new group targets SWIFT users
 A few months after hackers broke into Bangladesh's central bank and came close to getting away with $1 billion, researchers have uncovered evidence that a separate hacking group is targeting the same payment network.
A few months after hackers broke into Bangladesh's central bank and came close to getting away with $1 billion, researchers have uncovered evidence that a separate hacking group is targeting the same payment network.
The researchers, from security firm Symantec, said that they recently found new tools that target users of SWIFT, a payment network banks use to transfer payments that are sometimes in the range of hundreds of millions of dollars. The malicious tools monitor SWIFT messages sent to infected computers for International Bank Account Numbers or other keywords relating to specific transactions.
Read moreFastPOS malware abuses Windows Mailslots to steal POS data
 The group behind the FastPOS malware has updated their trojan with a new data exfiltration mechanism that abuses the Windows Mailslots mechanism to store data before exfiltration from infected systems.
The group behind the FastPOS malware has updated their trojan with a new data exfiltration mechanism that abuses the Windows Mailslots mechanism to store data before exfiltration from infected systems.
This new version of POS malware came to light this past summer when researchers discovered ads for it on underground carding forums. Analysis of the malware showed a new POS malware family that focused on speed and sacrificed stealth, an opposite approach to how most POS malware operate today. Trend Micro continued its analysis of this malware after the initial detection and discovered traces of FastPOS activity dating back to March 2015.
Read moreMarsJoke: the cryptor and the cure
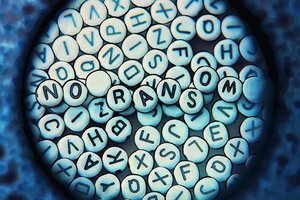 Every day, new versions and variations of ransomware pop up. Malware creators are still sure that ransomware is their ticket to easy street, despite the fact that law enforcement agencies are paying more and more attention to the problem.
Every day, new versions and variations of ransomware pop up. Malware creators are still sure that ransomware is their ticket to easy street, despite the fact that law enforcement agencies are paying more and more attention to the problem.
In fact, so many different versions are out there, ransomware creators have started to repeat themselves or copy the work of others. For example, the recently discovered Trojan-cryptor Polyglot, aka MarsJoke, is a knockoff of the infamous (and rather nasty) CTB-Locker ransomware. You can see traces of CTB-Locker all over Polyglot. Its interface is absurdly reminiscent of the older Trojan.
Read moreGuide for Pokémon Go Trojan catches Pokémon trainers
 Less than three months after Pokémon Go launched, criminals sneaked malware into Google Play to target Pokémon trainers. Experts discovered the Trojan several days ago and immediately reported it to Google.
Less than three months after Pokémon Go launched, criminals sneaked malware into Google Play to target Pokémon trainers. Experts discovered the Trojan several days ago and immediately reported it to Google.
Unfortunately, by that time, the malicious app called Guide for Pokémon Go had already been downloaded more than 500,000 times. In the past few months almost 6 million people gave Pokémon Go a try. It’s no wonder that the massively popular game quickly caught the attention of cybercriminals: The first malware for Pokémon Go was traced in July, soon after the launch of the game. At that time, the situation was not so dangerous.
Read moreMirai Trojan is the next big threat to IoT devices and Linux servers
 A new trojan named Mirai has surfaced, and it's targeting Linux servers and IoT devices, mainly DVRs, running Linux-based firmware, for the purpose of enslaving these systems as part of a large botnet used to launch DDoS attacks. Mirai is an evolution of an older trojan, also used for DDoS attacks.
A new trojan named Mirai has surfaced, and it's targeting Linux servers and IoT devices, mainly DVRs, running Linux-based firmware, for the purpose of enslaving these systems as part of a large botnet used to launch DDoS attacks. Mirai is an evolution of an older trojan, also used for DDoS attacks.
Mirai's mode of operation is largely the same as Gafgyt, targeting IoT devices running Busybox, a slimmed-down version of select GNU tools and libraries, usually deployed on small embedded hardware. The trojan also targets only a specific set of platforms, on which IoT devices are usually built.
Read moreBetabot password stealing trojan re-emerges with ransomware infecting capabilities
 Cybercrime is a constantly evolving entity as evidenced most recently in Betabot – a trojan that has been circulating in cyberspace for years in various forms. Betabot functioned in various capacities including as a banking trojan.
Cybercrime is a constantly evolving entity as evidenced most recently in Betabot – a trojan that has been circulating in cyberspace for years in various forms. Betabot functioned in various capacities including as a banking trojan.
Now, security researchers have uncovered that in addition to functioning as a password-stealing malware, Betabot has begun infecting users with ransomware. According to Invincea security researcher Pat Belcher, Betabot developers have created the "first known weaponised document" with password-stealing capabilities, which can also install Cerber ransomware as a second-stage attack.
Read moreNew Trojan SpyNote installs backdoor on Android devices
 A new Android Trojan called SpyNote has been identified by researchers who warn that attacks are forthcoming. The Trojan has not been spotted in any active campaigns. But expert believes because the software is now widely available on the Dark Web, that it will soon be used in a wave of upcoming attacks.
A new Android Trojan called SpyNote has been identified by researchers who warn that attacks are forthcoming. The Trojan has not been spotted in any active campaigns. But expert believes because the software is now widely available on the Dark Web, that it will soon be used in a wave of upcoming attacks.
Researchers say that’s where they found a malware builder tool specifically designed to be used to create multiple versions of SpyNote Trojan. SpyNote has a wide range of backdoor features that include the ability to view all messages on a device, eavesdrop on phone calls, activate the phone’s camera or microphone remotely or track the phone’s GPS location.
Read moreLurk banking trojan delivered via Ammyy website
 Hackers breached the official website of the popular remote administration tool Ammyy Admin and leveraged it to deliver Lurk and other pieces of malware. Lurk is a banking Trojan that has been used to target Russian financial institutions and other types of organizations.
Hackers breached the official website of the popular remote administration tool Ammyy Admin and leveraged it to deliver Lurk and other pieces of malware. Lurk is a banking Trojan that has been used to target Russian financial institutions and other types of organizations.
The threat has been around for five years and experts estimate that it has helped cybercrime gangs steal roughly $45 million. Russian authorities recently arrested 50 individuals suspected of using the malware and the arrests are believed to have led to the disappearance of the notorious Angler exploit kit. The Lurk Trojan has often been delivered via watering hole attacks.
Read moreNew Delilah trojan used to blackmail employees
 Threat intelligence experts from Diskin Advanced Technologies have discovered a new trojan that is exchanged in closed criminal groups and is currently being used to infect workers at different companies and blackmail them to provide information on their employer.
Threat intelligence experts from Diskin Advanced Technologies have discovered a new trojan that is exchanged in closed criminal groups and is currently being used to infect workers at different companies and blackmail them to provide information on their employer.
Named Delilah, this custom piece of malware is a backdoor trojan that infects workers who visit online adult and gaming sites. Once on the user's device, the trojan starts collecting information on its target. The crooks will amass vast amounts of data in an effort to gather as much information on the victim's family and workplace environment as possible.
Read moreCryptXXX ransomware will now steal your passwords as well
 The most recent version of the CryptXXX ransomware came with lots of changes, among which the most important is an infostealer module that can dump and steal passwords from various applications on the infected machine.
The most recent version of the CryptXXX ransomware came with lots of changes, among which the most important is an infostealer module that can dump and steal passwords from various applications on the infected machine.
Called StillerX, this module was seen part of CryptXXX, detected by Proofpoint for the first time on May 26. The US security firm says that this CryptXXX version comes with lots of new features, but StillerX makes it more dangerous than before. StillerX works just like classic password dumpers, also known as infostealers. CryptXXX's StillerX module is capable of targeting all sorts of software.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















