NSA tapped German Chancellery for decades, WikiLeaks claims
 The US National Security Agency tapped phone calls involving German chancellor Angela Merkel and her closest advisers for years and spied on the staff of her predecessors.
The US National Security Agency tapped phone calls involving German chancellor Angela Merkel and her closest advisers for years and spied on the staff of her predecessors.
A report released by the group suggested NSA spying on Merkel and her staff had gone on far longer and more widely than previously realised. WikiLeaks said the NSA targeted 125 phone numbers of top German officials for long-term surveillance. The release risks renewing tensions between Germany and the US a month after they sought to put a row over spying behind them, with Barack Obama declaring in Bavaria that the two nations were inseparable allies.
Read moreThe Justice Department could strike deal with Edward Snowden
 Former Attorney General Eric Holder said that a possibility exists for the Justice Department to cut a deal with former NSA contractor Edward Snowden that would allow him to return to the United States from Moscow.
Former Attorney General Eric Holder said that a possibility exists for the Justice Department to cut a deal with former NSA contractor Edward Snowden that would allow him to return to the United States from Moscow.
In an interview, Holder said we are in a different place as a result of the Snowden disclosures and that his actions spurred a necessary debate that prompted President Obama and Congress to change policies on the bulk collection of phone records of American citizens. Holder’s comments came as he began a new job as a private lawyer at Covington & Burling, where he worked before serving as the nation’s top law enforcement officer from February 2009 until last April.
Read moreMajor Adobe Flash security flaw discovered in Hacking Team leak
 Spyware company Hacking Team was compromised earlier this week, leading to 400GB of internal and files, source code, and emails being made available on torrent sites for anyone to download.
Spyware company Hacking Team was compromised earlier this week, leading to 400GB of internal and files, source code, and emails being made available on torrent sites for anyone to download.
While there’s some embarrassing communications contained within the leak, some serious software flaws have also been discovered. Some source code contained within the leak includes software vulnerabilities that are being exploited by Hacking Team to break into PCs. Two unpatched vulnerabilities have been discovered, affecting Adobe’s Flash software and Microsoft’s Windows operating system.
Read moreTechnologies that see through the walls
 In the beginning of 2015, there was a wave of publications on a handheld radar called RANGE-R that has been used by government services. The radar system is able to ‘see through the walls’, it registers motion inside closed spaces.
In the beginning of 2015, there was a wave of publications on a handheld radar called RANGE-R that has been used by government services. The radar system is able to ‘see through the walls’, it registers motion inside closed spaces.
The existence of such a device was surprising for many journalists tasked with publishing the features of RANGE-R. These radars have long been in mass production for military and intelligence-service needs. Prior to that, the technology was only available for some governmental services. Today, the radar system is more widely used due to technological advancements that contributed to price decreases.
Read moreScammers bypass Google filters with PDF cloaking
 Scammers have long used cloaking as a technique to drive up search engine rankings, stuffing webpages full of keywords and links that make them attractive to Google, but not to actual readers. Google wised up and those tactics became ineffective.
Scammers have long used cloaking as a technique to drive up search engine rankings, stuffing webpages full of keywords and links that make them attractive to Google, but not to actual readers. Google wised up and those tactics became ineffective.
But, according to a new report from SophosLabs, there is one twist on cloaking that still works, and that is to stuff those keywords and links into PDF documents instead. SophosLabs noticed the PDF cloaking a few days ago, and hundreds of thousands of fake PDF documents have been appearing daily since then. Each is stuffed with random keywords, as well as links to the other pages in the campaign.
Read moreOracle PeopleSoft attack could enable big data breaches
 Vulnerabilities in Oracle PeopleSoft systems could be enabling data breaches at businesses, government organizations and universities.
Vulnerabilities in Oracle PeopleSoft systems could be enabling data breaches at businesses, government organizations and universities.
Researchers have identified 549 Oracle PeopleSoft systems that are accessible via the internet, and observed that 231 of those systems are vulnerable to the TokenChpoken attack. The attack can ultimately be used to login under any account and gain full access to the PeopleSoft system, and it additionally opens the door for attacks against other systems and third-party data stores. One institution with PeopleSoft systems accessible via the internet is Harvard University, which announced an intrusion.
Read moreHacking Team hacked: firm sold spying tools to repressive regimes
 The cybersecurity firm Hacking Team appears to have itself been the victim of a hack, with documents that purport to show it sold software to repressive regimes being posted to the company’s own Twitter feed.
The cybersecurity firm Hacking Team appears to have itself been the victim of a hack, with documents that purport to show it sold software to repressive regimes being posted to the company’s own Twitter feed.
The Italy-based company offers security services to law enforcement and national security organisations. It offers legal offensive security services, using malware and vulnerabilities to gain access to target’s networks. According to the documents, Hacking Team has also been working with numerous repressive governments – something it has previously explicitly denied doing. It has not been possible to independently verify the veracity of the documents.
Read moreNew details emerge in Bitstamp's $5 million Bitcoin hack
 In a new document leaked from Bitstamp, one of the more popular Bitcoin exchanges in the world, the company details how a phishing attack several months ago bereft the company of roughly $5 million at then-current prices.
In a new document leaked from Bitstamp, one of the more popular Bitcoin exchanges in the world, the company details how a phishing attack several months ago bereft the company of roughly $5 million at then-current prices.
Beginning around page nine of the leaked report, which is clearly marked confidential but is already floating around numerous mirror sites since its initial leak, the document details how the company discovered an "ominous" and large data movement of around 3.5 gigabytes from Bitstamp's server to an IP in Germany. The company determined that it was their wallet.dat file that had gone over the tubes from their servers to some unknown.
Read moreWikileaks: US routinely spied on Brazil
 The Wikileaks website says it has evidence that a number of senior Brazilian government officials were routinely spied on by the National Security Agency in the United States. It says the NSA was particularly active in economic espionage against Brazil.
The Wikileaks website says it has evidence that a number of senior Brazilian government officials were routinely spied on by the National Security Agency in the United States. It says the NSA was particularly active in economic espionage against Brazil.
Wikileaks published a list of 29 phone numbers of Brazilians in banking, finance and the economy. According to the website the espionage apparently began in early 2011 or even earlier. President Dilma Rousseff cancelled a state visit to Washington two years ago when former CIA contractor Edward Snowden revealed that her phones and emails were being spied on.
Read moreMasterCard will approve purchases by scanning your face
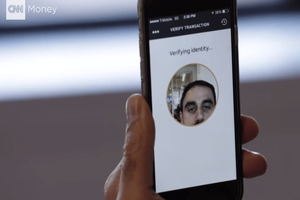 This fall, MasterCard will start experimenting with a new program: approving online purchases with a facial scan. At checkout, you'll be asked to hold up your phone and snap a photo. MasterCard's thinking? It's easier than remembering a password.
This fall, MasterCard will start experimenting with a new program: approving online purchases with a facial scan. At checkout, you'll be asked to hold up your phone and snap a photo. MasterCard's thinking? It's easier than remembering a password.
This is MasterCard's way of cutting down fraud. Currently, customers can set up something called "SecureCode," which requires a password when shopping online. This stops credit-card-number-stealing hackers from actually using your card on the Web. It was used in 3 billion transactions last year. But passwords get forgotten, stolen, or intercepted. So, banks are following Apple's lead.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















