Chechen leader (Russia) Ramzan Kadyrov offered Russia to be without foreign messengers
 Using Skype, Twitter and other western services harms the security of the country, says the head of Chechnya. Chechen leader Ramzan Kadyrov said that the spread of western communication services on the Internet harms national security.
Using Skype, Twitter and other western services harms the security of the country, says the head of Chechnya. Chechen leader Ramzan Kadyrov said that the spread of western communication services on the Internet harms national security.
Their use encourages the ongoing double standards west policy, Kadyrov said. He considers situation to be unacceptable in which the West controls Russian users, and Russia is far from the steering information. The main problem is lack of control. Kadyrov also offered to turn off the Internet, as a global network, in his opinion, interfere with the proper education of youth.
Read moreTwitter sues the government of the USA
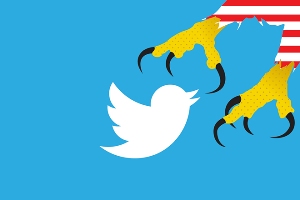 Twitter just sued the federal government over restrictions the government places on how much the company can disclose about surveillance requests it receives. For months, Twitter has tried to negotiate with the government to expand the kind of information that it and other companies are allowed to disclose. But it failed.
Twitter just sued the federal government over restrictions the government places on how much the company can disclose about surveillance requests it receives. For months, Twitter has tried to negotiate with the government to expand the kind of information that it and other companies are allowed to disclose. But it failed.
Twitter asserts in its suit that preventing the company from telling users how often the government submits national security requests for user data is a violation of the First Amendment. The move goes a step beyond a challenge filed by Google and other companies last year that also sought permission on First Amendment grounds to disclose how often it receives national security requests for data.
Read moreSocial Media and the ‘Spiral of Silence’
 A major insight into human behavior from pre-internet era studies of communication is the tendency of people not to speak up about policy issues in public—or among their family, friends, and work colleagues—when they believe their own point of view is not widely shared. This tendency is called the “spiral of silence”.
A major insight into human behavior from pre-internet era studies of communication is the tendency of people not to speak up about policy issues in public—or among their family, friends, and work colleagues—when they believe their own point of view is not widely shared. This tendency is called the “spiral of silence”.
Some social media creators and supporters have hoped that social media platforms like Facebook and Twitter might produce different enough discussion venues that those with minority views might feel freer to express their opinions, thus broadening public discourse and adding new perspectives to everyday discussion of political issues.
Read moreThink crypto hides you from spooks on Facebook? THINK AGAIN
 Activists just got another reason to worry about what spooks might be able to learn about them, with boffins demonstrating that a decent traffic fingerprint can tell an attacker what's going on, even if an app is defended by encryption.
Activists just got another reason to worry about what spooks might be able to learn about them, with boffins demonstrating that a decent traffic fingerprint can tell an attacker what's going on, even if an app is defended by encryption.
The researchers from the Universities of Padua and Rome have found that for activities like posting messages on a friend's Facebook wall, browsing a profile on a social network, or sending an e-mail, there's no need to decrypt an encrypted data flow. The researchers note that even in the hands of a knowledgeable user there are opportunities for “malicious adversaries willing to trace people … the adversary can still infer a significant amount of information from the properly encrypted traffic.”
Read moreAmerican military studies human behavior
 The Department of Defense of the USA makes experiments on social networks users. Defense Advanced Research Projects Agency provides monitoring of microblog service and Internet users‘ posts on such large social networks as Facebook, Twitter, Pinterest and Kickstarter.
The Department of Defense of the USA makes experiments on social networks users. Defense Advanced Research Projects Agency provides monitoring of microblog service and Internet users‘ posts on such large social networks as Facebook, Twitter, Pinterest and Kickstarter.
The Pentagon invests large amount of money for carrying out experiments which are connected with users‘ mood and its manipulation. Technological Department of Defence and scientists of university hold the Pentagon project, called Social Media in Strategic Communication. It provides monitoring of Twitter microblog service and Internet users‘ posts on large social networks.
Read moreThe Secret Service wants software that detects social media sarcasm.
 USA Secret Service reported that wants to buy analytical computer programs that are able to synthesize data from social media and provide this information in a visual form.
USA Secret Service reported that wants to buy analytical computer programs that are able to synthesize data from social media and provide this information in a visual form.
The orders ask for a long list of specific tools, including the ability to identify social media influencers, analyze data streams in real time, access old Twitter data and use heat maps. And it wants the software to be compatible with Internet Explorer 8. Then there's the request to sift through the heaps of snark on Twitter and other social media services: "Ability to detect sarcasm and false positives," the request reads.
Read moreRussian official’s threat to ban Twitter spurs fast backlash
 Comments on Friday by a top Russian telecoms official, suggesting that the country might soon block access to Twitter, met with a swift wave of condemnation — including from other government officials — providing a rare window into differences of opinion inside the Kremlin over how best to censor voices of dissent.
Comments on Friday by a top Russian telecoms official, suggesting that the country might soon block access to Twitter, met with a swift wave of condemnation — including from other government officials — providing a rare window into differences of opinion inside the Kremlin over how best to censor voices of dissent.
In an interview with a local newspaper Friday, Maxim Ksenzov, deputy head of the government’s telecommunications watchdog, Roskomnadzor, called Twitter a “political” tool that undermines the state’s authority. “We can block Twitter or Facebook tomorrow for several minutes,” Ksenzov said. “We do not see any risks in that.”
Read moreUS State Department used Twitter-like online service to undermine Cuba’s government
 The US government operated a Twitter-like social network to sow political discontent among Cubans.
The US government operated a Twitter-like social network to sow political discontent among Cubans.
The Associated Press revealed last week that the US government's Agency for International Development (USAID) established and operated a Twitter-like social network in Cuba over a period of two years starting in 2009. The main purpose of the program was to undermining the country's communist government.
Tomorrow, the head of USAID, Rajiv Shah will take a stand before a Senate subcommittee of foreign operations and State Department budget to answer some difficult questions about the program.
2 million passwords for Facebook, Twitter and Google posted online
 Over 2 million passwords for popular social networking sites such as Facebook and Twitter, as well as Google and Yahoo accounts have been stolen and posted online, with Russian social networks VKontakte and Odnoklassniki also featuring on the hitlist.
Over 2 million passwords for popular social networking sites such as Facebook and Twitter, as well as Google and Yahoo accounts have been stolen and posted online, with Russian social networks VKontakte and Odnoklassniki also featuring on the hitlist.
Internet security firm Trustwave exposed the extensive data hoard, saying in its blog that the responsible botnet – dubbed Pony – had harvested information from thousands of vulnerable computers on a global scale.
The information included login credentials, email addresses and passwords. In total, 1,580,000 website login credentials were stolen, alongside 320,000 email and 41,000 FTP accounts.
Read moreTwitter: 70% of requests for personal data come from the U.S.
 U.S. authorities are more likely to ask for personal information of a user's microblogging service Twitter. Over the past six months, the U.S. government sent 902 to the company requesting a statement. Twitter just received 1176 requests.
U.S. authorities are more likely to ask for personal information of a user's microblogging service Twitter. Over the past six months, the U.S. government sent 902 to the company requesting a statement. Twitter just received 1176 requests.
Thus, in the United States accounts for more than 70% of all claims, the report said. In second place at the request of information is Japan (87 requests), and the third - the United Kingdom (26 requests). A large number of requests from Turkey or Brazil have been reported to the company. In this case, Twitter is rarely receives requests to remove a certain message. In just six months, the company received 21 such a request, of which only two were initiated by the U.S. authorities.
Read more New secured zone of Google Play: secure messenger SafeUM for Android. Download, Install, Communicate
New secured zone of Google Play: secure messenger SafeUM for Android. Download, Install, Communicate
Axarhöfði 14,
110 Reykjavik, Iceland














