Snowden docs: British spies used DDoS attacks against Anonymous
 The British spy agency GCHQ used hacking techniques, including distributed denial of service (DDoS) attacks, against the hacking collective Anonymous, according to new documents leaked by Edward Snowden.
The British spy agency GCHQ used hacking techniques, including distributed denial of service (DDoS) attacks, against the hacking collective Anonymous, according to new documents leaked by Edward Snowden.
Anonymous hackers were attacking websites with their own DDoS attacks in 2011 while authorities in the UK and the U.S. were scrambling for a response — it turns out GCHQ's answer was to turn the hackers' weapons against them. The new documents reveal that a GCHQ unit dubbed the Joint Threat Research Intelligence Group, or JTRIG, launched an operation called Rolling Thunder against the hacker collective in 2011.
Read moreSnowden’s effect or now Twitter wants to “spy” on SMS and calls
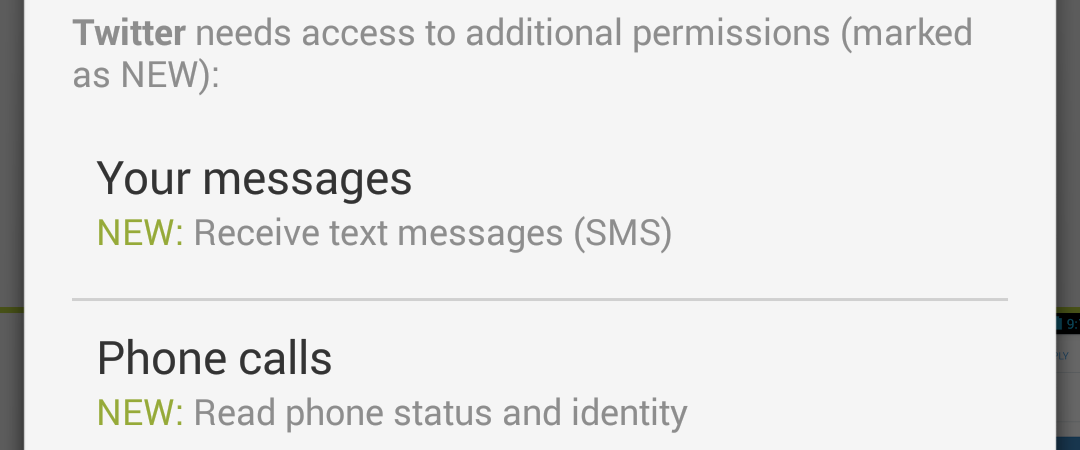 Mobile apps' “appetite” grows for users' private data. Attentive owners of Android may have noticed Twitter’s update request to gain access to SMS and phone status.
Mobile apps' “appetite” grows for users' private data. Attentive owners of Android may have noticed Twitter’s update request to gain access to SMS and phone status.
Previously similar attempts to access SMS have been already observed by Facebook, Viber, Hangouts and Telegram. They would explain such a move with making it easier for users to enter the activation code.
But it gets more difficult to explain this strange desire to access the status of you phone calls. Why would Twitter what to know when and who’s calling?
Read moreCanadian intelligence used airport Wi-Fi to spy on passengers
 After exposing scandalous spy programs of American and British intelligence services, Edward Snowden leaked some info on the Canadian Communications Security Establishment (CSEC).
After exposing scandalous spy programs of American and British intelligence services, Edward Snowden leaked some info on the Canadian Communications Security Establishment (CSEC).
According to top secret documents, leaked by former NSA contractor, CSEC agents used public Wi-Fi in one of the biggest airports of Canada to track wireless devices of thousands of passengers for days when they left the terminal. Data, collected by the surveillance program, included hotel, cafes, restaurants and other public places visited by passengers, as well as means of transportation.
Read moreU.S. creates a machine for blackmail
 Representatives of Obama‘s Administration continue to insist that spying on Americans is not a violation of constitutional rights of citizens and carried out exclusively in the interests of national security.
Representatives of Obama‘s Administration continue to insist that spying on Americans is not a violation of constitutional rights of citizens and carried out exclusively in the interests of national security.
However, Chris Kitts, the father of beforeitsnews.com, believes that the obtained information is used not only for security purposes.
According to Chris Kitts, Washington creates “The machine for the implementation blackmail. Now they have access to the emails of people who are in the data store in Utah.
Read moreSnowden says NSA engages in industrial espionage
 The U.S. National Security Agency is involved in industrial espionage and will grab any intelligence it can get its hands on regardless of its value to national security, former NSA contractor Edward Snowden told a German TV network.
The U.S. National Security Agency is involved in industrial espionage and will grab any intelligence it can get its hands on regardless of its value to national security, former NSA contractor Edward Snowden told a German TV network.
In text released ahead of a lengthy interview to be broadcast on Sunday, ARD TV quoted Snowden saying the NSA does not limit its espionage to issues of national security and he cited German engineering firm, Siemens as one target. "If there's information at Siemens that's beneficial to U.S. national interests - even if it doesn't have anything to do with national security - then they'll take that information nevertheless," Snowden said, according to ARD, which recorded the interview in Russia where he has claimed asylum.
Read moreObama NSA reform speech promises modest changes
 President Barack Obama on Friday laid out a vision of modest changes for the National Security Agency in a speech that will likely please neither reformers nor agency defenders.
President Barack Obama on Friday laid out a vision of modest changes for the National Security Agency in a speech that will likely please neither reformers nor agency defenders.
The speech, which took place in the Great Hall of the Justice Department building, came more than seven months after the leaks from former NSA contractor Edward Snowden began. Acknowledging the public clamor those leaks have generated, the president nonetheless defended many of the agency's most controversial programs as necessary in the fight against terrorism. "The task before us now is greater than simply repairing the damage done to our operations; or preventing more disclosures from taking place in the future."
Read moreAnonymous search tool DuckDuckGo answered 1bn queries in 2013
.jpg) DuckDuckGo, the privacy-focused search engine, served over 1bn searches in 2013 after a huge surge in interest following the Snowden revelations. Until Edward Snowden's files detailing the extent of state surveillance, the search engine received around 1.5m queries per day. But in the weeks and months following the Guardian's publication of the NSA files, the number of users more than doubled.
DuckDuckGo, the privacy-focused search engine, served over 1bn searches in 2013 after a huge surge in interest following the Snowden revelations. Until Edward Snowden's files detailing the extent of state surveillance, the search engine received around 1.5m queries per day. But in the weeks and months following the Guardian's publication of the NSA files, the number of users more than doubled.
By November, more than 4 million people were using the site every day, and on Tuesday 7 January the site had its biggest day so far, serving 4,452,957 queries in a 24-hour period. "Needless to say, it was a great year for us," DuckDuckGo said in a blogpost. "We're looking forward to similar greatness in 2014.
Read moreUS Senator Rand Paul to Sue President Obama Over NSA Spying
 Republican senator Rand Paul has announced plans to sue US President Barack Obama over Edward Snowden's revelations of unlawful spying by the National Security Agency (NSA).
Republican senator Rand Paul has announced plans to sue US President Barack Obama over Edward Snowden's revelations of unlawful spying by the National Security Agency (NSA).
Paul said he is urging all US citizens with mobile phones to join a group action aimed at preventing Obama from "snooping on the American people". Paul said the legal action is also aimed at protecting the Fourth Amendment to the US constitution, which prevents unreasonable searches and seizures, and sending a message to the US government that it cannot continue to access ordinary citizens' phone and email records without permission or a warrant.
Read moreNSA statement does not deny 'spying' on members of Congress
 The National Security Agency on Saturday released a statement in answer to questions from a senator about whether it “has spied, or is … currently spying, on members of Congress or other American elected officials”, in which it did not deny collecting communications from legislators of the US Congress to whom it says it is accountable.
The National Security Agency on Saturday released a statement in answer to questions from a senator about whether it “has spied, or is … currently spying, on members of Congress or other American elected officials”, in which it did not deny collecting communications from legislators of the US Congress to whom it says it is accountable.
In a letter dated 3 January, Senator Bernie Sanders of Vermont defined “spying” as “gathering metadata on calls made from official or personal phones, content from websites visited or emails sent, or collecting any other data from a third party not made available to the general public in the regular course of business”.
Read moreNSA can turn your iPhone into a spy, says privacy advocate Jacob Appelbaum
 The NSA can plant malicious software on Apple's iPhone, turning one of the world's most popular smartphones into a pocket-sized spy, according to a leading security expert.
The NSA can plant malicious software on Apple's iPhone, turning one of the world's most popular smartphones into a pocket-sized spy, according to a leading security expert.
Privacy advocate Jacob Appelbaum gave the public an unusually explicit peek into the intelligence world's toolbox at a hacking conference in Germany, pulling back the curtain on the US National Security Agency's (NSA) arsenal of high-tech spy gear.
The independent journalist and security expert said on Monday that the NSA could turn iPhones into eavesdropping tools and use radar wave devices to harvest electronic information from computers, even if they weren't online.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















