This phishing attack is almost impossible to detect on Chrome, Firefox and Opera
 A Chinese infosec researcher has reported about an "almost impossible to detect" phishing attack that can be used to trick even the most careful users on the Internet.
A Chinese infosec researcher has reported about an "almost impossible to detect" phishing attack that can be used to trick even the most careful users on the Internet.
He warned, hackers can use a known vulnerability in the Chrome, Firefox and Opera web browsers to display their fake domain names as the websites of legitimate services, like Apple, Google, or Amazon to steal login or financial credentials and other sensitive information from users. What is the best defence against phishing attack? Generally, checking the address bar after the page has loaded and if it is being served over a valid HTTPS connection. Right?
Read moreSkype users hit by ransomware through in-app malicious ads
 Several users have complained that ads served through Microsoft's Skype app are serving malicious downloads, which if opened, can trigger ransomware.
Several users have complained that ads served through Microsoft's Skype app are serving malicious downloads, which if opened, can trigger ransomware.
News of the issue came from a Reddit thread, in which the original poster said that Skype's home screen -- the first screen that shows up on consumer versions of the software -- was pushing a fake, malicious ad, purporting to be a critical update for the Flash web plug-in. According to the thread, the ad triggered a download of an HTML application, designed to look like a legitimate app. The app, when opened, would download a malicious payload, which locks the user's computer and encrypts its files for ransom.
Read moreAviation-related phishing campaigns seeking credentials
 A wave of email-based phishing campaigns is targeting airline consumers with messages that contain malware that infects systems or links to spoofed airline websites that are personalized to trick victims into handing over personal or business credentials. “Over the past several weeks, we have seen a combination of attack techniques.
A wave of email-based phishing campaigns is targeting airline consumers with messages that contain malware that infects systems or links to spoofed airline websites that are personalized to trick victims into handing over personal or business credentials. “Over the past several weeks, we have seen a combination of attack techniques.
One, where an attacker impersonates a travel agency or someone inside a company. Recipients are told an email contains an airline ticket or e-ticket,” said Asaf Cidon, vice president, content security services at Barracuda Networks. Attachments, he said, are documents rigged with malware or are designed to download it from a command and control server.
Read moreSomeone is putting lots of work into hacking Github developers
 Open-source developers who use Github are in the cross-hairs of advanced malware that can steal passwords, download sensitive files, take screenshots, and self-destruct when necessary.
Open-source developers who use Github are in the cross-hairs of advanced malware that can steal passwords, download sensitive files, take screenshots, and self-destruct when necessary.
Dimnie, as the reconnaissance and espionage trojan is known, has largely flown under the radar for the past three years. It mostly targeted Russians until early this year, when a new campaign took aim at multiple owners of Github repositories. One commenter in this thread reported the initial infection e-mail was sent to an address that was used solely for Github, and researchers told they have no evidence it targeted anyone other than Github developers.
Read moreAdware rewrites phone details for legitimate security software on Google search
 A new adware family changes the contact details of legitimate security companies in search results to promote tech support scams.
A new adware family changes the contact details of legitimate security companies in search results to promote tech support scams.
Dubbed Crusader, the adware is often installed as part of nuisanceware and free software bundles, downloading itself as a free browser extension for Chrome, a Firefox add-on, and Internet Explorer Browser Helper Object. When executed, the malware requests permissions to read and change the information on websites you visit, and should the user grant permission, their entire internet traffic is at risk of exploit or manipulation. Crusader pulls instructions from a configuration file downloaded after a user is infected.
Read moreHackers using fake cellphone towers to spread Android banking trojan
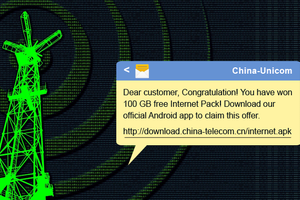 Chinese Hackers have taken Smishing attack to the next level, using rogue cell phone towers to distribute Android banking malware via spoofed SMS messages.
Chinese Hackers have taken Smishing attack to the next level, using rogue cell phone towers to distribute Android banking malware via spoofed SMS messages.
SMiShing — phishing attacks sent via SMS — is a type of attack wherein fraudsters use number spoofing attack to send convincing bogus messages to trick mobile users into downloading a malware app onto their smartphones or lures victims into giving up sensitive information. Security researchers have uncovered that Chinese hackers are using fake base transceiver stations to distribute "Swearing Trojan," an Android banking malware that once appeared neutralized after its authors were arrested in a police raid.
Read moreUS charges Lithuanian man with $100 million email fraud
 U.S. prosecutors have charged a Lithuanian man with engaging in an email fraud scheme in which he bilked two U.S.-based companies out of more than $100 million by posing as an Asian hardware vendor. Evaldas Rimasauskas was arrested late last week by Lithuanian authorities.
U.S. prosecutors have charged a Lithuanian man with engaging in an email fraud scheme in which he bilked two U.S.-based companies out of more than $100 million by posing as an Asian hardware vendor. Evaldas Rimasauskas was arrested late last week by Lithuanian authorities.
Rimasauskas does not yet have legal counsel, a spokesman for the prosecutors said. The alleged scheme is an example of a growing type of fraud called "business email compromise," in which fraudsters ask for money using emails targeted at companies that work with foreign suppliers or regularly make wire transfers.
Read moreHackers: We will remotely wipe iPhones unless Apple pays ransom
 A hacker or group of hackers is apparently trying to extort Apple over alleged access to a large cache of iCloud and other Apple email accounts. The hackers, who identified themselves as 'Turkish Crime Family', demanded $75,000 in Bitcoin or Ethereum, another increasingly popular crypto-currency, or $100,000 worth of iTunes gift cards in exchange for deleting the alleged cache of data.
A hacker or group of hackers is apparently trying to extort Apple over alleged access to a large cache of iCloud and other Apple email accounts. The hackers, who identified themselves as 'Turkish Crime Family', demanded $75,000 in Bitcoin or Ethereum, another increasingly popular crypto-currency, or $100,000 worth of iTunes gift cards in exchange for deleting the alleged cache of data.
"I just want my money and thought this would be an interesting report that a lot of Apple customers would be interested in reading and hearing," one of the hackers told. The hackers provided screenshots of alleged emails between the group and members of Apple's security team.
Read moreCriminals move card cloning business to clearnet, launch new, faster device
 Criminal groups are becoming more and more sophisticated, especially when it comes to the hi-tech devices they put to use. One of these groups, called The CC Buddies, has recently launched a new contactless card cloning device and it's not even bothering to hide its business on the dark web anymore.
Criminal groups are becoming more and more sophisticated, especially when it comes to the hi-tech devices they put to use. One of these groups, called The CC Buddies, has recently launched a new contactless card cloning device and it's not even bothering to hide its business on the dark web anymore.
"We're happy to announce the Infusion X6 is out," reads an email sent out by the group. The device can be used to "capture bank cards" up to 15 centimeters away and to save up to 21 cards per second. That's a clear upgrade from the Infusion X5 which they were selling last summer, which could copy up to 15 bank cards per second.
Read moreNew fileless malware uses DNS queries to receive PowerShell commands
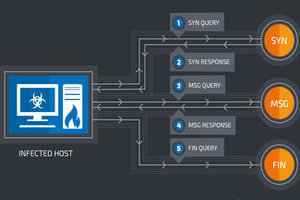 It is no secret that cybercriminals are becoming dramatically more adept, innovative, and stealthy with each passing day. While new forms of cybercrime are on the rise, traditional activities seem to be shifting towards more clandestine techniques that involve the exploitation of standard system tools and protocols, which are not always monitored.
It is no secret that cybercriminals are becoming dramatically more adept, innovative, and stealthy with each passing day. While new forms of cybercrime are on the rise, traditional activities seem to be shifting towards more clandestine techniques that involve the exploitation of standard system tools and protocols, which are not always monitored.
The latest example of such attack is DNSMessenger – a new Remote Access Trojan that uses DNS queries to conduct malicious PowerShell commands on compromised computers – a technique that makes the RAT difficult to detect onto targeted systems. The Trojan came to the attention of Cisco's Talos threat research group by a security researcher named Simpo, who highlighted a tweet that encoded text in a PowerShell script that said 'SourceFireSux.'
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















