Hackers attack Gmail users
 Having pretended to be Gmail Account Services hackers send harmful emails to account owners.
Having pretended to be Gmail Account Services hackers send harmful emails to account owners.
According to the researches of the Chinese security software company, called Trend Micro, hackers have launched a campaign, which gives itself as Google‘s support service and is directed against users of Gmail service. Hackers work in such a way: the victim gets email allegedly from Gmail Account Services in which the owner of an account is informed on the unknown user authorization in his account with the help of unrecognizable device. The expert of the Trend Micro Company Jay Yaneza noted that the email can really be confused with the original notice of Gmail; however the knowing and attentive user will be able to find some differences.
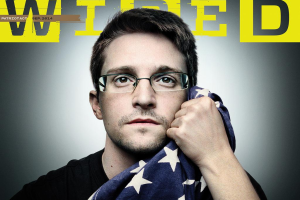
Read moreNSA is working on 'MonsterMind' cyberwar bot
 NSA project called MonsterMind that would give the agency control of all internet traffic entering the US, the ability to detect and block attacks in progress, and potentially, some day, the power to autonomously launch retaliatory strikes without human intervention.
NSA project called MonsterMind that would give the agency control of all internet traffic entering the US, the ability to detect and block attacks in progress, and potentially, some day, the power to autonomously launch retaliatory strikes without human intervention.
Snowden says that the program is currently in development, but he gave no information on when or even if it might be deployed. If MonsterMind does become reality, it would encompass even greater US control over the internet than that which now exists, as well as ever more trampling on Fourth Amendment rights against unreasonable search.
Read moreJulian Assange is going to leave the shelter in the Ecuadorian Embassy
 "I can confirm I will be leaving the embassy soon", Julian Assange told a press-conference in the Ecuadorian Embassy in London.
"I can confirm I will be leaving the embassy soon", Julian Assange told a press-conference in the Ecuadorian Embassy in London.
But that would not be for reasons of health. He also said he would not hand himself over to the British police. The Wikileaks whistleblower repeated his protestations of innocence over claims made against him in Sweden over allegations of rape. The Wikileaks founder said he had not been charged with anything in Sweden or the UK and that the basis of his asylum was the US Justice Department's bid to charge him with espionage. For two years, Julian Assange has remained inside the white painted rooms of Ecuador’s embassy in London.
Read moreLeaks, lies and the bottom line
 Leaks like this not only show up all the time, they've increased in number over the years -- and now that it's easy to start anonymous rumors without accountability, our inboxes will simply give up. We are becoming a leak-obsessed culture.
Leaks like this not only show up all the time, they've increased in number over the years -- and now that it's easy to start anonymous rumors without accountability, our inboxes will simply give up. We are becoming a leak-obsessed culture.
Nearly everyone wants to know about tomorrow's devices, today, and few (if any) smartphones get launched without someone spilling the beans. The next iPhone hasn't even been announced yet, but millions of people already think they know what it looks like and what it will do, thanks to images of its supposed chassis, casing and sapphire display. Even if the leaks aren't accurate, it's too late -- there are likely plenty of folks who have already (bizarrely) decided whether to buy it or not.
Read moreElite US hackers shut down Syrian internet trying to snoop on traffic
 An elite team of US government hackers left Syria without internet, when they tried to hack one of the cores routers but instead crashed it, NSA whistleblower Edward Snowden said.
An elite team of US government hackers left Syria without internet, when they tried to hack one of the cores routers but instead crashed it, NSA whistleblower Edward Snowden said.
The three-day nationwide internet blackout in war-torn Syria in November 2012, which was blamed on either the government or the rebels, depending on who you listened to, was actually the doing of the Tailored Access Operations (TAO), a group of hackers in the employment of the US National Security Agency. And more more interesting.
Read moreMicrosoft doesn’t support Skype for Windows Phone 7
 Everybody who installs software on Windows Phone 7 personal mobile devices for won’t be authorized. In few weeks, Microsoft is going to stop supporting Skype for Windows Phone 7 devices. According to the technical support program site, software will not be available "in any form" for the seventh version of mobile platform.
Everybody who installs software on Windows Phone 7 personal mobile devices for won’t be authorized. In few weeks, Microsoft is going to stop supporting Skype for Windows Phone 7 devices. According to the technical support program site, software will not be available "in any form" for the seventh version of mobile platform.
In the report, the company warns that users who have already installed Skype on their mobile devices running Windows Phone 7 will no longer be able to go through the authorization process in service. According to Microsoft, the reason for the refusal to renovate the support program for Windows Phone 7 is the desire “to provide users with a better version of Skype”.
Read moreTwitter: 23 million active users are actually bots
 A new SEC filing says more than 8% of the accounts on the social media site are automated. While these bots may provide some kind of public service information, they may also be created to drum up buzz about a company or artificially boost a user's number of followers.
A new SEC filing says more than 8% of the accounts on the social media site are automated. While these bots may provide some kind of public service information, they may also be created to drum up buzz about a company or artificially boost a user's number of followers.
The social network currently has 271 million active users but, according to a new filing with the Security and Exchange Commission, over 8% of them aren't operated by humans. One of Twitter's big selling points, whether it be to music fans, grass roots political activists, sports obsessives, movie buffs or journalists, is that it breaks down the barriers between you and the person or the subject that most interests or excites you.
Read moreApple started negotiations with the medical companies for HealthKit
 In anticipation of the launch of the new operating system iOS 8, the company Apple started negotiations with working in health organizations about the deployment of the service HealthKit.
In anticipation of the launch of the new operating system iOS 8, the company Apple started negotiations with working in health organizations about the deployment of the service HealthKit.
Platform HealthKit, presented at the developer conference WWDC 2014 will allow to gather in one place from a variety of sources of data on the user’s vital signs, including pulse, blood pressure, cholesterol and sugar, the amount of steps you’ve walked and calories burned, and make recommendations to maintain your health and even notify the attending physician in the case of the emergence of anxiety symptoms. Service HealthKit, as the application Health, integrated into iOS, 8, which will be released this fall.
Read moreSmart Nest thermostat turned into spying device in 15 minutes
 At this year's edition of the Black Hat security conference, a group of researchers has shown how extremely easy is to hack into the smart thermostats manufactured by Nest.
At this year's edition of the Black Hat security conference, a group of researchers has shown how extremely easy is to hack into the smart thermostats manufactured by Nest.
When Google acquired home automation company Nest earlier this year, many voiced their privacy concerns regarding the increased scope of Google's data mining via Nest's smart thermostats and smoke detectors. But the danger might be even more immediate, as a group of researchers have demonstrated at this year's edition of the Black Hat security conference. Independent researcher Daniel Buentello, and researechers Yier Jin and Grant Hernandez of the University of Central Florida, have discovered that the OS level security checks that should prevent the installation of malware on the device can be easily bypassed.
Read moreCloudBot is a free, malwareless, alternative to traditional Botnets
 Researchers take advantage of cloud service providers' free trials and lousy anti-automation controls to use cloud instances like bots.
Researchers take advantage of cloud service providers' free trials and lousy anti-automation controls to use cloud instances like bots.
Thrifty attackers, are you tired of investing your dollars in a botnet that's constantly being disrupted by new anti-virus signatures and bot downtime? A "cloudbot" might be just what you seek. As shown at Black Hat last week by Rob Ragan and Oscar Salazar, senior security associates at Bishop Fox, cloudbots are entirely free and very resilient, and they offer all the uptime of a cloud service with no need for malware. Good news for bot masters working on the cheap.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















