How the NSA built its own secret Google
 The National Security Agency is secretly providing data to nearly two dozen U.S. government agencies with a “Google-like” search engine built to share more than 850 billion records about phone calls, emails, cellphone locations and internet chats.
The National Security Agency is secretly providing data to nearly two dozen U.S. government agencies with a “Google-like” search engine built to share more than 850 billion records about phone calls, emails, cellphone locations and internet chats.
The documents provide the first definitive evidence that the NSA has for years made massive amounts of surveillance data directly accessible to domestic law enforcement agencies. Planning documents for ICREACH, as the search engine is called, cite the Federal Bureau of Investigation and the Drug Enforcement Administration as key participants. ICREACH contains information on the private communications of foreigners and it appears.
Read moreFacebook to fix flaw that can force iPhones to make calls
 Facebook will soon be pushing out an update to its iOS Messenger app meant to patch a vulnerability that could allow attackers to place pricy calls from users' phones by simply making them click on a web link.
Facebook will soon be pushing out an update to its iOS Messenger app meant to patch a vulnerability that could allow attackers to place pricy calls from users' phones by simply making them click on a web link.
The flaw has been recently discovered by developer Andrei Neculaesei from Copenhagen, and can be triggered by using the tel URL scheme. "The tel URL scheme is used to launch the Phone app on iOS devices and initiate dialing of the specified phone number," it is explained in an Apple document. "When a user taps a telephone link in a webpage, iOS displays an alert asking if the user really wants to dial the phone number and initiates dialing if the user accepts.
Read moreResearchers Find Security Flaws in Backscatter X-ray Scanners
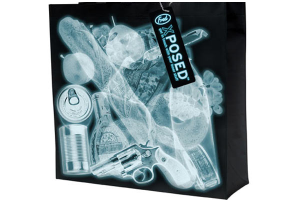 A team of researchers from the University of California, San Diego, the University of Michigan, and Johns Hopkins University have discovered several security vulnerabilities in full-body backscatter X-ray scanners deployed to U.S. airports between 2009 and 2013.
A team of researchers from the University of California, San Diego, the University of Michigan, and Johns Hopkins University have discovered several security vulnerabilities in full-body backscatter X-ray scanners deployed to U.S. airports between 2009 and 2013.
In laboratory tests, the team was able to successfully conceal firearms and plastic explosive simulants from the Rapiscan Secure 1000 scanner. The team was also able to modify the scanner operating software so it presents an “all-clear” image to the operator even when contraband was detected. Professor Hovav Shacham stands in front of the backscatter x-ray scanner as you would during a security check.
Read moreBrazil wants no Secret on app stores
 A Brazilian judge has called for Apple and Google to remove the anonymous social network Secret from their app stores and wipe it from phones on which it has already been installed across the country.
A Brazilian judge has called for Apple and Google to remove the anonymous social network Secret from their app stores and wipe it from phones on which it has already been installed across the country.
The San Francisco startup has come under fire from those charging that Secret and other anonymous apps too easily become sanctuaries for cyberbullying. Last week, a San Diego man started a Change.org petition seeking to remove Secret from Apple and Android app stores, though the petition had little support. On Monday, an opinion piece in the New York Times argued that anonymous apps and Internet websites such as Secret often make women and minorities a target for attack.
Read moreCHS Hacked via Heartbleed Vulnerability
 As many of you may have already been aware, a breach at Community Health Systems (CHS) affecting an estimated 4.5 million patients was recently revealed. TrustedSec obtained the first details on how the breach occured and new information relating to this breach.
As many of you may have already been aware, a breach at Community Health Systems (CHS) affecting an estimated 4.5 million patients was recently revealed. TrustedSec obtained the first details on how the breach occured and new information relating to this breach.
The initial attack vector was through the infamous OpenSSL “heartbleed” vulnerability which led to the compromise of the information. This confirmation of the initial attack vector was obtained from a trusted and anonymous source close to the CHS investigation. Attackers were able to glean user credentials from memory on a CHS Juniper device via the heartbleed vulnerability.
Read moreCryptolocker flogged on YouTube
 Cryptolocker is being flogged over YouTube by vxers who have bought advertising space, researchers Vadim Kotov and Rahul Kashyap have found. The researchers made the discovery while monitoring YouTube and website banners for instances where malware writers had actually purchased space to foist their wares on unpatched web users.
Cryptolocker is being flogged over YouTube by vxers who have bought advertising space, researchers Vadim Kotov and Rahul Kashyap have found. The researchers made the discovery while monitoring YouTube and website banners for instances where malware writers had actually purchased space to foist their wares on unpatched web users.
The duo who will present at the upcoming Virus Bulletin 2014 conference in Seattle wrote in a paper advertisement networks was a viable way to flog virus and trojans.
Read moreNorton antivirus overhauls consumer products from 9 to 1
 Beginning Sept. 23, Symantec will shift from having nine versions of its consumer-oriented Norton antivirus program to just one — Norton Security. "We're kind of catching up with our customers," said Fran Rosch,vice president of Norton's business unit.
Beginning Sept. 23, Symantec will shift from having nine versions of its consumer-oriented Norton antivirus program to just one — Norton Security. "We're kind of catching up with our customers," said Fran Rosch,vice president of Norton's business unit.
"When they call in and we ask them 'Which Norton product do you have?' they always just say 'I have Norton.'" Norton is computer security giant Symantec's consumer-oriented division. Using something akin to the Netflix model, the program will allow each customer to sign up for one account which can be applied to multiple devices, including desktop and laptop computers, smartphones and tablets.
Read moreXiaomi Phones send personal data to Chinese servers
 According to the experts, the devices retrieved messages and photos, even though the backup feature was off. Information security experts of many countries have criticized the Chinese telecommunication equipment suppliers for installing backdoors in their products, that’s why the Chinese company Xiaomi, which is engaged in production of smartphones, was sued.
According to the experts, the devices retrieved messages and photos, even though the backup feature was off. Information security experts of many countries have criticized the Chinese telecommunication equipment suppliers for installing backdoors in their products, that’s why the Chinese company Xiaomi, which is engaged in production of smartphones, was sued.
In the judicial claim the Chinese manufacturer was accused of secretly taking users‘ personal information and then sending SMS, files from gallery, the list of contacts, IMEI, IMSI and so on to servers in Beijing. Besides, data were copied without owner‘s permission even thus the backup feature was disabled.
Read moreThink crypto hides you from spooks on Facebook? THINK AGAIN
 Activists just got another reason to worry about what spooks might be able to learn about them, with boffins demonstrating that a decent traffic fingerprint can tell an attacker what's going on, even if an app is defended by encryption.
Activists just got another reason to worry about what spooks might be able to learn about them, with boffins demonstrating that a decent traffic fingerprint can tell an attacker what's going on, even if an app is defended by encryption.
The researchers from the Universities of Padua and Rome have found that for activities like posting messages on a friend's Facebook wall, browsing a profile on a social network, or sending an e-mail, there's no need to decrypt an encrypted data flow. The researchers note that even in the hands of a knowledgeable user there are opportunities for “malicious adversaries willing to trace people … the adversary can still infer a significant amount of information from the properly encrypted traffic.”
Read moreYour smartphone can spy on you without permission
 Your Android phone can be turned into a microphone without your permission or knowledge. All that’s needed are the gyros in your phone that measure orientation. Stanford researchers have shown how to rewire them to pick up sound waves.
Your Android phone can be turned into a microphone without your permission or knowledge. All that’s needed are the gyros in your phone that measure orientation. Stanford researchers have shown how to rewire them to pick up sound waves.
Together with the defense firm Rafael, they created an Android app called Gyrophone, which shows just how easy it is to get the vibrating pressure plates used by the gyroscope to pick up vibrations of sound at frequencies in the 80-250Hz range – the base frequencies of the human voice. “We show that the MEMS gyroscopes found on modern smartphones are sufficiently sensitive to measure acoustic signals in the vicinity of the phone.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















