Your anonymous posts to Secret aren’t anonymous after all
 White hat hacker Ben Caudill is halfway through his sandwich when he casually reaches over to his iPhone, swipes the screen a few times, then holds it up to me. “Is that you?” he asks.
White hat hacker Ben Caudill is halfway through his sandwich when he casually reaches over to his iPhone, swipes the screen a few times, then holds it up to me. “Is that you?” he asks.
It is, but nobody was supposed to know. He’s showing me one of my posts to Secret, the popular anonymous sharing app that lets you confess your darkest secrets to your friends without anyone knowing it’s you. A few minutes ago I gave Caudill my personal e-mail address, and that was all he needed to discover my secret in the middle of a Palo Alto diner, while eating a BLT. My secret is pretty lame, but Secret’s stream is slurry of flippant posts, Silicon Valley gossip, and genuinely personally confessions like.
Read moreCryptoWall ransomware scam rakes in $1 MEEELLION
 Victims of the CryptoWall ransomware have been extorted out of at least $1m. Despite a takedown operation in June, CryptoWall continues to be the largest and most destructive ransomware threat on the internet, according to the latest analysis of the threat by security researchers from Dell SecureWorks Counter Threat Unit.
Victims of the CryptoWall ransomware have been extorted out of at least $1m. Despite a takedown operation in June, CryptoWall continues to be the largest and most destructive ransomware threat on the internet, according to the latest analysis of the threat by security researchers from Dell SecureWorks Counter Threat Unit.
Cryptowall is a strain of file-encrypting ransomware that encrypts files on infected Windows PCs and attached storage devices with RSA-2048 encryption before demanding a ransom for the private key that recovers the documents. Dell SecureWorks CTU researchers registered a domain used by the CryptoWall malware as a backup command and control (C2) server in February.
Read moreThe Government of the USA uses NSA ‘Google’ to access data records
 The US National Security Agency (NSA) shares vast amounts of communications data with the country’s government agencies using a search engine similar to Google.
The US National Security Agency (NSA) shares vast amounts of communications data with the country’s government agencies using a search engine similar to Google.
NSA’s search tool, called ICREACH, makes “more than 850 billion records about phone calls, emails, cellphone locations and internet chats” available to nearly two dozen US government agencies, including the Federal Bureau of Investigation (FBI) and the Central Intelligence Agency (CIA), The Intercept reported on Tuesday citing classified documents leaked by NSA whistleblower Edward Snowden.
Read moreExperts have found vulnerability in Yo
 Russian hackers were able to get access to the accounts of many users. Alexander Grebenshikov and Leo Loktionov, information security specialists told about the presence of a dangerous gap in the Yo messenger.
Russian hackers were able to get access to the accounts of many users. Alexander Grebenshikov and Leo Loktionov, information security specialists told about the presence of a dangerous gap in the Yo messenger.
Experts said that if you update the account login application, the system sends a confirmation code to the mobile number by default, without making sure that it really belongs to the owner of the account. Information security experts explained that on the Yo Password Reset page, one may write any user‘s name and get a link to change the password, by using and entering your own phone number. Alexander Grebenshikov noticed this kind of vulnerability, while Leo Loktionov found a way with the help of which one may get account using the panel of service creators.
Read moreGoogle dorks – FBI warning about dangerous ‘new’ search tool
 The FBI has issued a warning to police and other emergency response personnel about a lethal new tool which ‘malicious actors’ have been using to deadly effect against American government institutions – Google dorks.
The FBI has issued a warning to police and other emergency response personnel about a lethal new tool which ‘malicious actors’ have been using to deadly effect against American government institutions – Google dorks.
The warning refers specifically to ‘Google dorks’ or “Google dorking” – ie the use of specialized search syntax, using terms such as “filetype:sql”. ‘Google dorks’ refers to search syntax which allow users to search within a specific website (using the term in:url) or for specific file types, and can thus be used to search databases. Such search terms are widely known, and legal – the warning alerts units who may not be aware of the technique to secure databases properly.
Read moreA map of everyone using the Internet
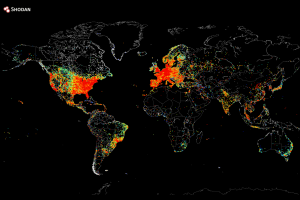 What you're looking at is a map of nearly every device that was connected to the internet on August 2. Or, at least, a map of ones that responded to a ping request from John Matherly, an internet cartographer. Because now, you can ping every computer on the internet fairly easily.
What you're looking at is a map of nearly every device that was connected to the internet on August 2. Or, at least, a map of ones that responded to a ping request from John Matherly, an internet cartographer. Because now, you can ping every computer on the internet fairly easily.
And you can make a map just like this without all that much technical knowledge. Within the last year, it has become exceedingly easy to scan the entire internet using open source tools. Using a method known as "stateless scanning," you can send and receive packets to, well, everyone connected to the internet on the planet, in roughly an hour, as we reported last summer.
Read moreExperts from Dr.Web have found a new Trojan.Mayachok
 The problem is that Trojan shows advertising to users and at the same time reads the information from the computer. Experts have found a new threat from Trojans, marked Trojan.Mayachok 18831, it extends with the help of e-mail sending.
The problem is that Trojan shows advertising to users and at the same time reads the information from the computer. Experts have found a new threat from Trojans, marked Trojan.Mayachok 18831, it extends with the help of e-mail sending.
After starting on the infected device, Trojan.Mayachok 18831 verifies presence of the duplicate at which identification ceases to function in system. Moreover, malware makes search of active anti-virus programs and sends found information to the server of malefactors. Then Trojan obtains data on the house folder of the Windows user, tries to read the configuration file which was created earlier. If the attempt isn’t successful, it will start using its own installations.
Read moreFBI suspects Russian hackers of data theft from JPMorgan

“The way the Russians do it, to the extent we can see into the process, is they encourage certain targets,” James Lewis, the director of the Strategic Technologies program at the Center for Strategic and International Studies in Washington, was quoted as saying by Bloomberg. “The Russians typically keep open the options to do something more, and the question now is what would trigger that and what would our response be,” he added.
Read moreSocial Media and the ‘Spiral of Silence’
 A major insight into human behavior from pre-internet era studies of communication is the tendency of people not to speak up about policy issues in public—or among their family, friends, and work colleagues—when they believe their own point of view is not widely shared. This tendency is called the “spiral of silence”.
A major insight into human behavior from pre-internet era studies of communication is the tendency of people not to speak up about policy issues in public—or among their family, friends, and work colleagues—when they believe their own point of view is not widely shared. This tendency is called the “spiral of silence”.
Some social media creators and supporters have hoped that social media platforms like Facebook and Twitter might produce different enough discussion venues that those with minority views might feel freer to express their opinions, thus broadening public discourse and adding new perspectives to everyday discussion of political issues.
Read moreChina plans to launch own OS to compete with Microsoft, Google, and Apple
 China is looking to launch its own operating system, an initiative that the government reportedly hopes will make its information systems more secure. Ni Guangnan, of the Chinese Academy of Engineering, the country's state-run engineering arm, says the new Chinese operating system could be launched as early as October.
China is looking to launch its own operating system, an initiative that the government reportedly hopes will make its information systems more secure. Ni Guangnan, of the Chinese Academy of Engineering, the country's state-run engineering arm, says the new Chinese operating system could be launched as early as October.
Details regarding the underpinnings of the operating system have yet to be revealed, but the move was reportedly spurred by the end of support of Windows XP and the ban on Windows 8 in China. The government also launched an anti-monopoly probe against Microsoft earlier this year.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















