Researchers Get $10,000 for Hacking Google Server with Malicious XML
 A critical vulnerability has been uncovered in Google that could allow an attacker to access the internal files of Google’s production servers.
A critical vulnerability has been uncovered in Google that could allow an attacker to access the internal files of Google’s production servers.
Sounds ridiculous but has been proven by the security researchers from Detectify.
The team of researchers found a loophole after they noticed that Google Toolbar Button Gallery allows users to customize their toolbars with new buttons. So, for the developers, it is easy to create their own buttons by uploading XML files containing metadata for styling and other such properties. This feature of Google search engine is vulnerable to XML External Entity.
Read moreTCP/IP might have been secure from the start if not for the NSA
 "The pervasiveness of the NSA's spying operation has turned it into a kind of bugaboo — the monster lurking behind every locked networking closet and the invisible hand behind every flawed crypto implementation.
"The pervasiveness of the NSA's spying operation has turned it into a kind of bugaboo — the monster lurking behind every locked networking closet and the invisible hand behind every flawed crypto implementation.
Those inclined to don the tinfoil cap won't be reassured by Vint Cerf's offhand observation in a Google Hangout on Wednesday that, back in the mid 1970s, the world's favorite intelligence agency may have also stood in the way of stronger network layer security being a part of the original specification for TCP/IP. (Video with time code.) Researchers at the time were working on just such a lightweight cryptosystem. On Stanford's campus, Cerf noted that Whit Diffie and Martin Hellman had researched and published a paper that described the functioning of a public key cryptography system.
Read moreHow advertising cookies let observers follow you across the web
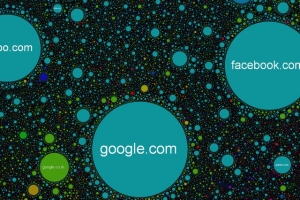 Back in December, documents revealed the NSA had been using Google's ad-tracking cookies to follow browsers across the web, effectively coopting ad networks into surveillance networks.
Back in December, documents revealed the NSA had been using Google's ad-tracking cookies to follow browsers across the web, effectively coopting ad networks into surveillance networks.
A new paper from computer scientists at Princeton breaks down exactly how easy it is, even without the resources and access of the NSA. The researchers were able to reconstuct as much as 90% of a user's web activity just from monitoring traffic to ad-trackers like Google's DoubleClick. Crucially, the researchers didn't need any special access to the ad data. They just sat back and watched public traffic across the network. As it turns out, trackers are displaying a surprising amount of information in public.
Read moreGoogle: the authorities are increasingly requesting access to data
 Representatives of Google said that the number of applications for authorities of different countries with requests for information has increased in the last four years 120%.
Representatives of Google said that the number of applications for authorities of different countries with requests for information has increased in the last four years 120%.
Increase the number of appeals is often associated with growth in the number of Google users, however representatives of the company say that the authorities more and more countries are trying to get the information they need from the Internet giant. In this connection Google again offered to develop the main principles of providing information to public authorities. The message of the company has made 53 356 inquiries relating to company data. Most of the calls came from the U.S. authorities, but these figures do not reflect mass monitoring of electronic communications, the Agency of national safety of the USA (NSA).
Read moreTop journalists and news companies are targets for hackers, contracted by state
 Google security experts suggest that hacker attacks on the world largest media companies are most likely “sponsored” by state.
Google security experts suggest that hacker attacks on the world largest media companies are most likely “sponsored” by state.
Google security engineers, speaking at the annual Black Hat hackers conference in Singapore, reported that 21 of the top 25 news organisations in the world have been attacked by hackers. Shane Huntley and Morgan Marquis-Boire suggested that those hackers are likely sponsored by foreign governments seeking information.
Researches said that many journalists and media companies are becoming more aware of cyber threats while the tech industry is falling behind managing online secure requirements. Apparently state-sponsored hacker attacks became governments' regular practice.
Read moreYour favorite Android Apps may have been mining Bitcoin without your knowledge

Researchers said they have uncovered two apps that were downloaded from the official Google Play market more than one million times that use Android devices to mine the Litecoin and Dogecoin cryptocurrencies without explicitly informing end users.
According Trend Micro, a researcher from antivirus provider the apps are Songs, installed from one million to five million times, and Prized, which was installed from 10,000 to 50,000 times. Neither the app descriptions nor their terms of service make clear that the apps subject Android devices to the compute-intensive process of mining, Trend Micro Mobile Threats Analyst Veo Zhang wrote. As of Wednesday afternoon, the apps were still available.
Read moreInternet spying threatens democracy, says Google's Larry Page
 Google chief executive Larry Page has condemned US government snooping on the internet as a threat to democracy. His comments came during an on-stage chat at a TED gathering, where a day earlier fellow Google founder Sergey Brin had a virtual encounter with National Security Agency leaker Edward Snowden.
Google chief executive Larry Page has condemned US government snooping on the internet as a threat to democracy. His comments came during an on-stage chat at a TED gathering, where a day earlier fellow Google founder Sergey Brin had a virtual encounter with National Security Agency leaker Edward Snowden.
A photo of Brin smiling with a robot remotely controlled by Snowden from his refuge in Russia, where the wanted man is in hiding, was tweeted by TED curator Chris Anderson and became an instant online hit. Advertisement "It is tremendously disappointing that the government sort of secretly did all this stuff and didn't tell us," Page said. He reasoned that details of suspected terrorist threats should remain cloaked but that the parameters of what US intelligence agents do, along with how and why they do it, should be public.
Read moreGoogle now encrypts Gmail traffic to and from its servers
 Google today filled one more privacy and security hole in its Gmail email service by encrypting all message traffic between email users, the search engine giant's email servers, and its data centers.
Google today filled one more privacy and security hole in its Gmail email service by encrypting all message traffic between email users, the search engine giant's email servers, and its data centers.
The full HTTPS encryption move was the next logical step to protecting Gmail users from the snooping eyes of government or malicious actors. "Starting today, Gmail will always use an encrypted HTTPS connection when you check or send email. Gmail has supported HTTPS since the day it launched, and in 2010 we made HTTPS the default. Today's change means that no one can listen in on your messages as they go back and forth between you and Gmail's servers--no matter if you're using public WiFi or logging in from your computer, phone or tablet," said Nicolas Lidzborski, Gmail Security Engineering Lead, in a blog post announcing the move.
Read morePrivacy becomes a luxury good
 LAST year, I spent more than $2,200 and countless hours trying to protect my privacy. Some of the items I bought — a $230 service that encrypted my data in the Internet cloud; a $35 privacy filter to shield my laptop screen from coffee-shop voyeurs; and a $420 subscription to a portable Internet service to bypass untrusted connections — protect me from criminals and hackers. Other products, like a $5-a-month service that provides me with disposable email addresses and phone numbers, protect me against the legal (but, to me, unfair) mining and sale of my personal data.
LAST year, I spent more than $2,200 and countless hours trying to protect my privacy. Some of the items I bought — a $230 service that encrypted my data in the Internet cloud; a $35 privacy filter to shield my laptop screen from coffee-shop voyeurs; and a $420 subscription to a portable Internet service to bypass untrusted connections — protect me from criminals and hackers. Other products, like a $5-a-month service that provides me with disposable email addresses and phone numbers, protect me against the legal (but, to me, unfair) mining and sale of my personal data.
In our data-saturated economy, privacy is becoming a luxury good. After all, as the saying goes, if you aren’t paying for the product, you are the product. And currently, we aren’t paying for very much of our technology.
Read moreGoogle, Facebook, Microsoft, Yahoo release details of US government data requests
 Facebook, Microsoft, Yahoo and Google on Monday began publishing details about the number of secret government requests for data they receive, hoping to show limited involvement in controversial U.S. surveillance efforts.
Facebook, Microsoft, Yahoo and Google on Monday began publishing details about the number of secret government requests for data they receive, hoping to show limited involvement in controversial U.S. surveillance efforts.
The tech industry has pushed for greater transparency on government data requests, seeking to shake off concerns about their involvement in vast, surreptitious surveillance programs revealed last summer by former spy contractor Edward Snowden. The government said last month it would relax rules restricting what details companies can disclose about Foreign Intelligence Surveillance Act (FISA) court orders they receive for user information.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















