NSA masqueraded as Google to spy on web users
 The NSA used ‘man in the middle’ hack attacks to impersonate Google and fool web users, leaks have revealed. The technique circumvents encryption by redirecting users to a copycat site which relays all the data entered to NSA data banks.
The NSA used ‘man in the middle’ hack attacks to impersonate Google and fool web users, leaks have revealed. The technique circumvents encryption by redirecting users to a copycat site which relays all the data entered to NSA data banks.
Brazilian television network Globo News released a report based on classified data divulged by former CIA worker Edward Snowden on Sunday. The report itself blew the whistle on US government spying on Brazilian oil giant Petrobras, but hidden in amongst the data was information the NSA had impersonated Google to get its hands on user data.
Read moreGoogle Jet Fleet loses a Pentagon fuel perk
 Google Inc. founders Larry Page and Sergey Brin may have to dig deeper to operate their fleet of private jets, after the U.S.
Google Inc. founders Larry Page and Sergey Brin may have to dig deeper to operate their fleet of private jets, after the U.S.
The agreement between the Google founders and the government, which started in 2007, ended Aug. 31 after officials at the National Aeronautics and Space Administration—which sponsored the arrangement—opted not to renew it, according to a Pentagon spokeswoman. The move followed discussions earlier this year between the Pentagon and NASA over whether the Google founders may have exceeded contract terms by using fuel for non-government flights.
Read moreEx-MI6 deputy chief plays down damage caused by Snowden leaks
 A former senior British secret intelligence officer on Thursday played down any potential damage done by the leaks to the Guardian of the spying activities of GCHQ and America's National Security Agency, apparently contradicting claims made by UK security chiefs.
A former senior British secret intelligence officer on Thursday played down any potential damage done by the leaks to the Guardian of the spying activities of GCHQ and America's National Security Agency, apparently contradicting claims made by UK security chiefs.
The leaks, by former NSA contractor Edward Snowden were "very embarrassing, uncomfortable, and unfortunate", Nigel Inkster, former deputy chief of MI6, said. While Inkster said it was too early to draw any definite conclusions about the impact of the leaks, he added: "I sense that those most interested in the activities of the NSA and GCHQ have not been told very much they didn't know already or could have inferred."
Read moreNSA shares raw intelligence including Americans' data with Israel
 The National Security Agency routinely shares raw intelligence data with Israel without first sifting it to remove information about US citizens, a top-secret document provided to the Guardian by whistleblower Edward Snowden reveals.
The National Security Agency routinely shares raw intelligence data with Israel without first sifting it to remove information about US citizens, a top-secret document provided to the Guardian by whistleblower Edward Snowden reveals.
Details of the intelligence-sharing agreement are laid out in a memorandum of understanding between the NSA and its Israeli counterpart that shows the US government handed over intercepted communications likely to contain phone calls and emails of American citizens. The agreement places no legally binding limits on the use of the data by the Israelis.
Read moreShodan, the search engine that points hackers directly to your webcam
 The U.S. Federal Trade Commission issued a complaint on Wednesday against Internet-connected device maker Trendnet due to a security flaw in one of its webcams – a device marketed for home security and baby monitoring – that let hackers spy on people in their homes.
The U.S. Federal Trade Commission issued a complaint on Wednesday against Internet-connected device maker Trendnet due to a security flaw in one of its webcams – a device marketed for home security and baby monitoring – that let hackers spy on people in their homes.
The complaint is the first issued by the FTC that concerns a device included in the category we know as the “Internet of Things.” But thanks to a specialized search engine for Internet-connected devices called Shodan, the FTC’s Trendnet complaint is likely only the beginning. Countless devices, ranging from webcams to electrical power plants, are insecurely connected to the Internet, making them vulnerable to hacker intrusions and other cyberattacks.
Read moreHow the NSA accesses smartphone data
 The US intelligence agency NSA has been taking advantage of the smartphone boom. It has developed the ability to hack into iPhones, android devices and even the BlackBerry, previously believed to be particularly secure.
The US intelligence agency NSA has been taking advantage of the smartphone boom. It has developed the ability to hack into iPhones, android devices and even the BlackBerry, previously believed to be particularly secure.
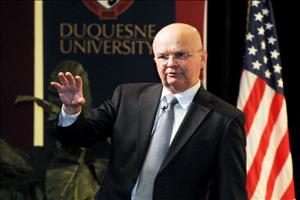
Michael Hayden has an interesting story to tell about the iPhone. He and his wife were in an Apple store in Virginia, Hayden, the former head of the NSA, said at a conference in Washington recently. A salesman approached and raved about the iPhone, saying that there were already "400,000 apps" for the device. Hayden, amused, turned to his wife and quietly asked: "This kid doesn't know who I am, does he? Four-hundred-thousand apps means 400,000 possibilities for attacks."
Read moreMicrosoft, Google sue USA for right to reveal nature of surveillance requests
 Microsoft and Google announced Friday they are going forward with a lawsuit against the US government for the right to reveal more information about official requests for customer data by American intelligence.
Microsoft and Google announced Friday they are going forward with a lawsuit against the US government for the right to reveal more information about official requests for customer data by American intelligence.
The companies originally filed suits in June following revelations provided by Edward Snowden of their relationship with the National Security Agency and the Foreign Intelligence Surveillance Court, which oversees the government’s requests of the companies’ systems. Microsoft’s general counsel Brad Smith announced the companies were following through with a suit, saying negotiations with the government since June have not yielded significant progress.
Read moreOhio Authorities residents secretly downloaded spyware to data of all driving licenses
 Ohio Attorney General Mike Devine at a press conference told reporters on the existence of a powerful facial recognition software that can access the database license. Photos from ID, he said, were secretly transferred to the police.
Ohio Attorney General Mike Devine at a press conference told reporters on the existence of a powerful facial recognition software that can access the database license. Photos from ID, he said, were secretly transferred to the police.
How does the photos were in the program is unknown. The system compares the faces of the people on driving licenses with CCTV footage and photographs of offenders detained in police stations. Devine said that the police have successfully used the new technology of data processing from June 2 of this year. During that time, were carried more than 2.6 million search queries. The program is aimed at more efficient use of surveillance cameras, wrote Raw Story.
Read moreNSA spied on United Nations
 The German magazine Der Spiegel says the U.S. National Security Agency secretly monitored the U.N.'s internal video conferencing system by decrypting it last year.
The German magazine Der Spiegel says the U.S. National Security Agency secretly monitored the U.N.'s internal video conferencing system by decrypting it last year.
The report is one of many developments that have come to light since former NSA contractor Edward Snowden leaked national security documents to the press, revealing a government surveillance program called PRISM that collected metadata over telecommunications lines. The newspaper said Sunday that documents it obtained from Snowden show the NSA decoded the system at the U.N.'s headquarters in New York last summer.
Read moreNSA officers use their spying power on love interests
 The National Security Agency admitted in a statement Friday that there have been “very rare” instances of willful violations of agency protocols by agency officers. Some of those willful violations involved officials turning their private eyes on love interests.
The National Security Agency admitted in a statement Friday that there have been “very rare” instances of willful violations of agency protocols by agency officers. Some of those willful violations involved officials turning their private eyes on love interests.
The practice isn’t frequent — one official estimated a handful of cases in the last decade — but it’s common enough to garner its own spycraft label: LOVEINT. Spy agencies often refer to their various types of intelligence collection with the suffix of “INT,” such as “SIGINT” for collecting signals intelligence, or communications; and “HUMINT” for human intelligence, or spying.
Read moreAxarhöfði 14,
110 Reykjavik, Iceland















